Ensuring privacy of users of social networks is probably an unsolvable conundrum. At the same time, an informed use of the existing privacy options by the social network participants may alleviate -or even prevent -some of the more... more
Ensuring privacy of users of social networks is probably an unsolvable conundrum. At the same time, an informed use of the existing privacy options by the social network participants may alleviate -or even prevent -some of the more... more
ICT is widely adopted by Asian youth and is utilized by people of all ages across the continent. Despite its many advantages, unethical ICT usage can lead to many complications. A harmful application of ICT for social communication and... more
The rapid growth of social media in recent years has fed into some highly undesirable phenomena such as proliferation of abusive and offensive language on the Internet. Previous research suggests that such hateful content tends to come... more
The rapid growth of social media in recent years has fed into some highly undesirable phenomena such as proliferation of hateful and offensive language on the Internet. Previous research suggests that such abusive content tends to come... more
The article is devoted to determining the types of youth content in social networks produced by political power subjects. The study's empirical base is the accounts of the social network Vkontakte, which are politically oriented towards... more
Automatic Text Classification is a machine learning task that automatically assigns a given text document to a set of pre-defined categories based on the features extracted from its textual content. Most online communication forums,... more
The Internet has revolutionized the way Americans process information. Social media platforms such as Twitter and Facebook have enabled discourse among citizens in a way never before possible. Often, these discussions are largely driven... more
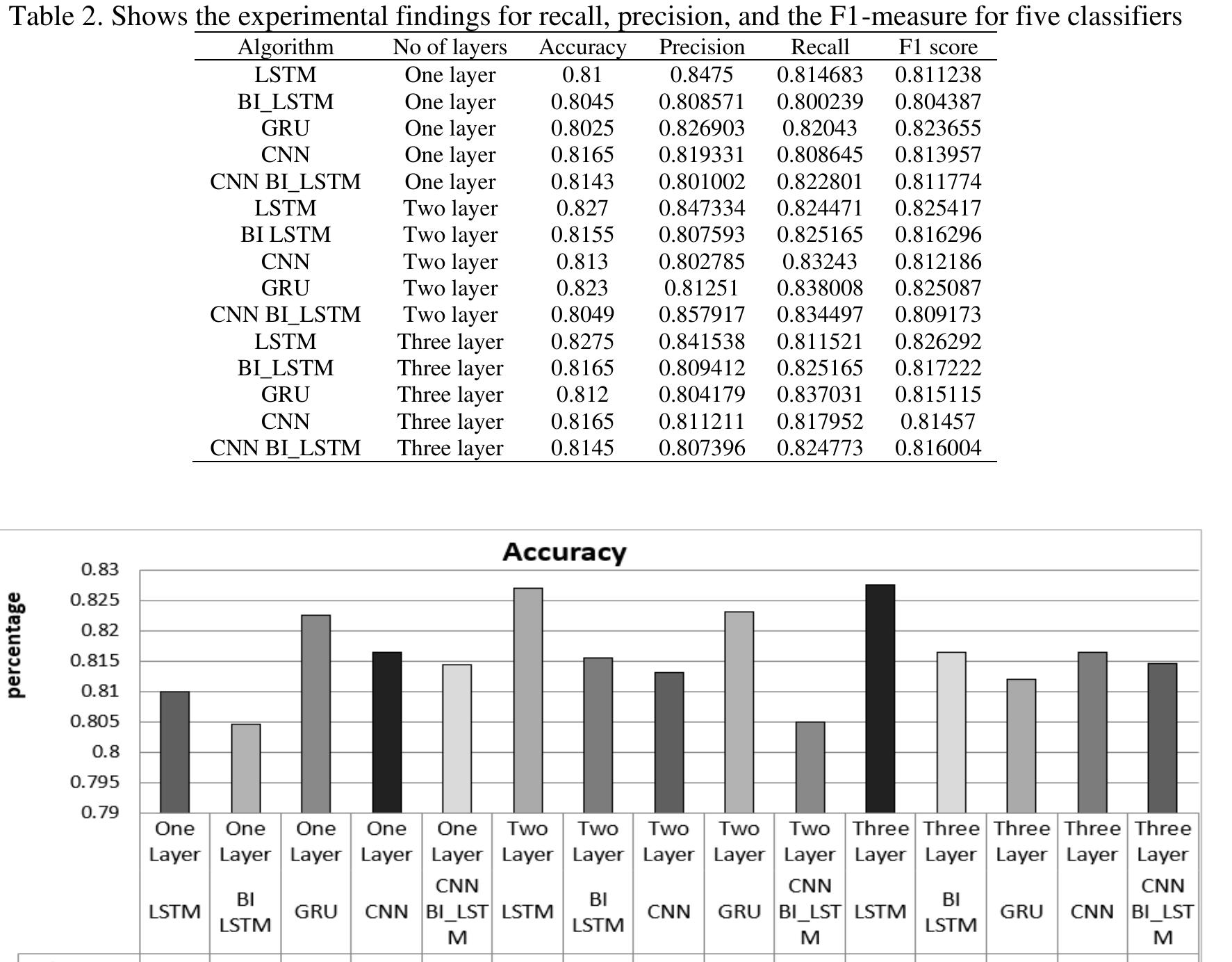
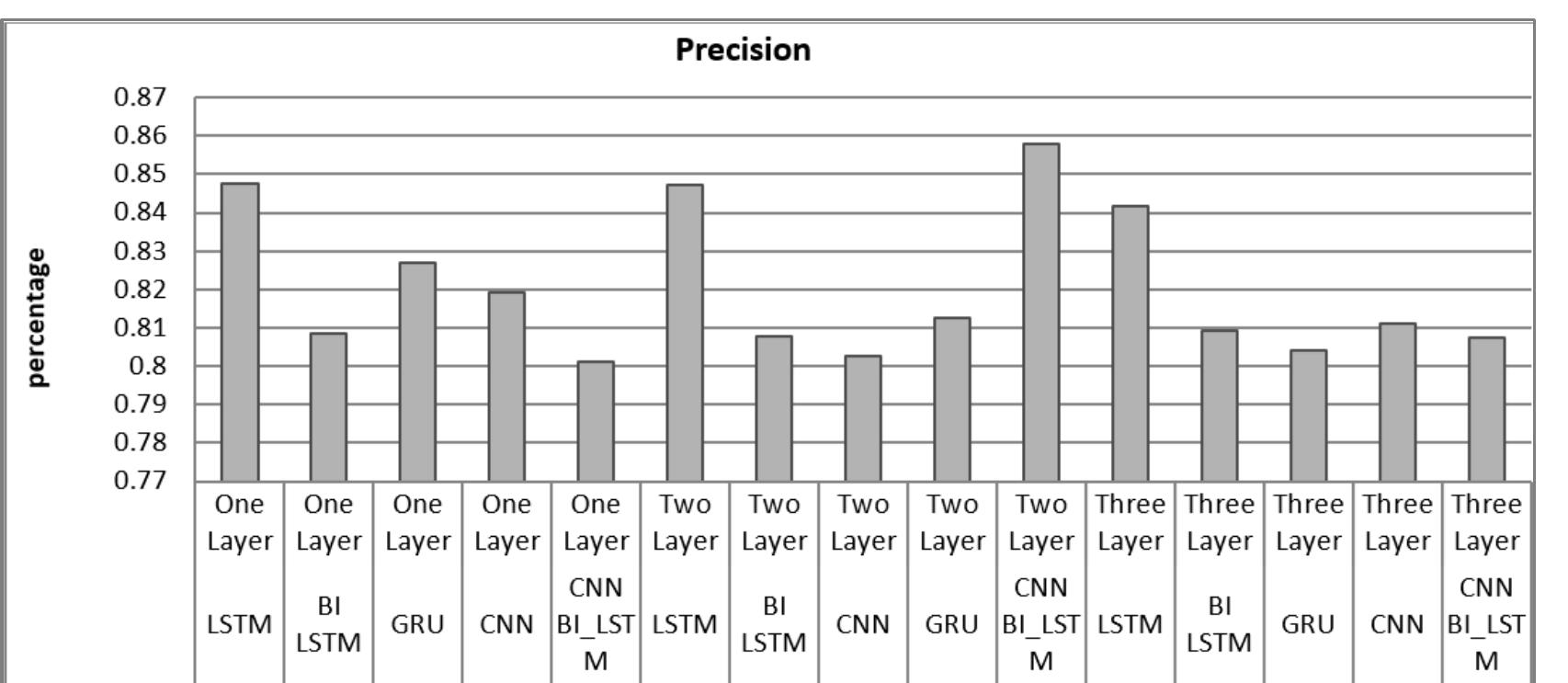
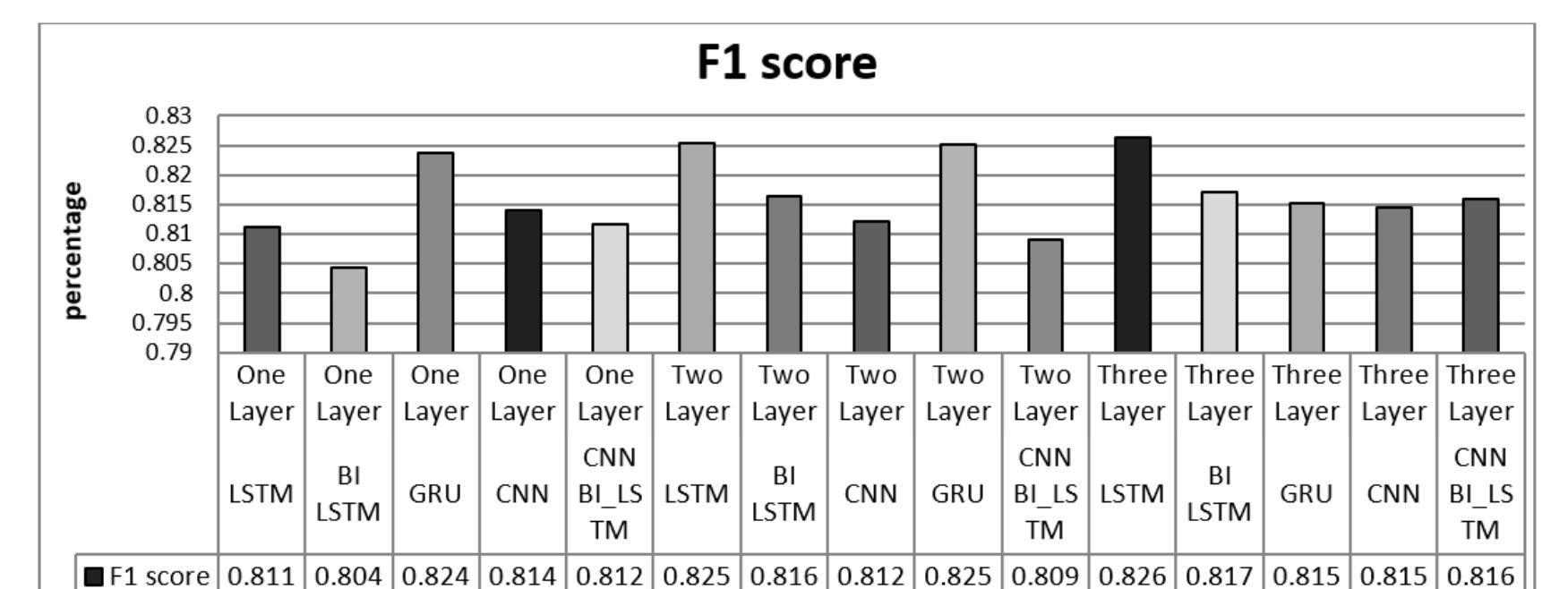
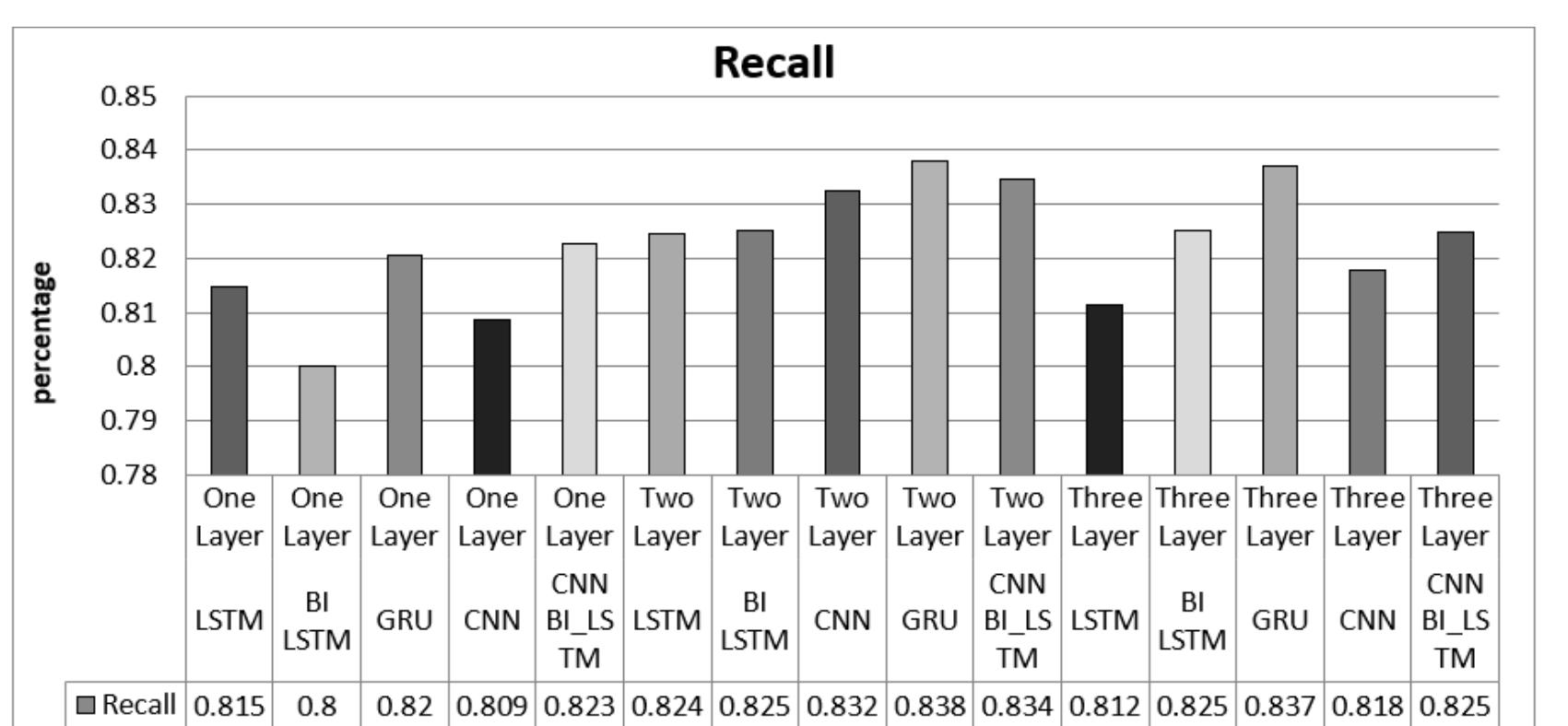
The widespread use of social media has escalated concerns about cyberbullying. Traditional methods for detecting and managing cyberbullying struggle with the sheer volume of electronic text data. This has led to the exploration of deep... more
How well can hate speech concept be abstracted in order to inform automatic classification in codeswitched texts by machine learning classifiers? We explore different representations and empirically evaluate their predictiveness using... more
How well can hate speech concept be abstracted in order to inform automatic classification in codeswitched texts by machine learning classifiers? We explore different representations and empirically evaluate their predictiveness using... more
People feel entitled to express their opinions on social media, and many of these opinions may be hostile to others. Hate speech recognition is essential in today's world, where it is important to keep track of what is posted in public... more
The wealth of opinions expressed in micro-blogs, such as tweets, motivated researchers to develop techniques for automatic opinion detection. However, accuracies of such techniques are still limited. Moreover, current techniques focus on... more
The advancement of social media plays an important role in increasing the population of youngsters on the web. And it has become the biggest medium of expressing one's thoughts and emotions. Recent studies report that cyberbullying... more
Social media has affected people's information sources. Since most of the news on social media is not verified by a central authority, it may contain fake news for various reasons such as advertising and propaganda. Considering an average... more
Antisocial behavior is a personality disorder that has characteristics such as repetitive actions that violate social norms, deceit and lying, impulsiveness, irritability and aggression, reckless disregard for the safety of oneself and... more
Since the textual contents on online social media are highly unstructured, informal, and often misspelled, existing research on message-level offensive language detection cannot accurately detect offensive content. This feature of the... more
Controversies are an inseparable part of social systems which, if constructed properly, can create a unique condition for higher-order learning. In addition, design inquiry, as a process of thought and planning, is also a constructive... more
Twitter is a social media platform and has become a go to place for young and old to express their views in short digital text format. This has made Twitter a source of big data of millions of small tweets. This mini project tries to... more
There are growing signs of discontent with the antisocial behavior expressed on social media platforms. Harnessing the power of machine learning for the purpose of detecting and mediating the spread of malicious behavior has received a... more
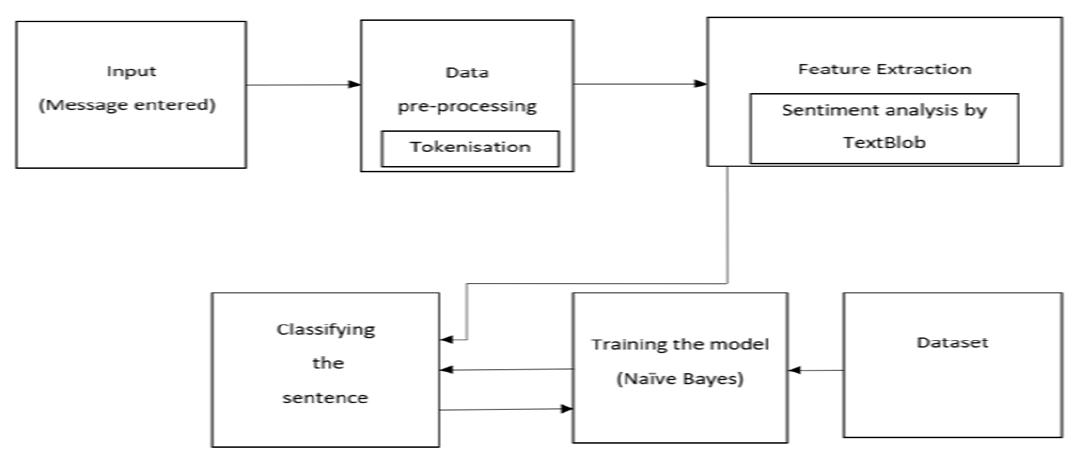
Sentiment Analysis, often known as opinion mining, is the technique of determining whether text data is positive, neutral, or negative using natural language processing, computer linguistics, and related technology. Hate Speech, on the... more
Sentiment analysis mainly supports sorting out the polarity and provides valuable information with the use of raw data in social media platforms. Many fields like health, business, and security require real-time data analysis for instant... more
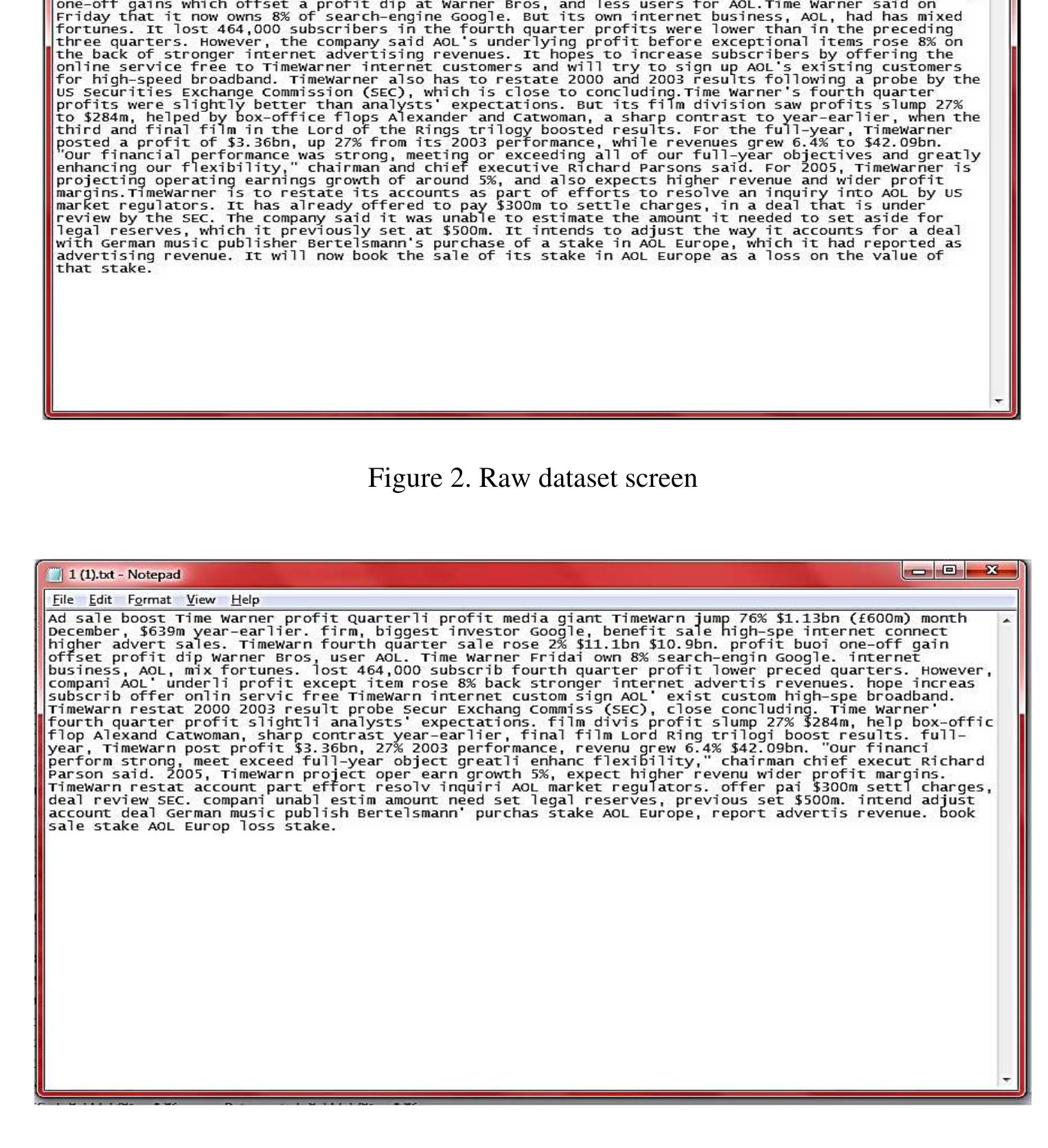
Social networks have ensured the expanding disproportion between the face of WWW stored traditionally in search engine repositories and the actual ever changing face of Web. Exponential growth of web users and the ease with which they can... more
Hate-speech detection on social network language has become one of the main researching fields recently due to the spreading of social networks like Facebook and Twitter. In Vietnam, the threat of offensive and harassment cause bad... more
Socialiniai tinklai-greitai populiarėjanti informacijos sklaidos priemonė. Pastebima, kad socialiniai tinklai paaugliams yra traukos vieta. Dažnas ir ilgas paauglių prisijungimas prie socialinių tinklų skatina priklausomybę. Tyrimo... more
Vytauto Didžiojo universitetasK. Donelaičio g. 58 LT-44248 KaunasTel. (8 37) 32 78 20El. paštas: [email protected] tinklai – greitai populiarėjanti informacijos sklaidos priemonė. Pastebima, kad socialiniai tinklai... more
Sentiment Analysis, often known as opinion mining, is the technique of determining whether text data is positive, neutral, or negative using natural language processing, computer linguistics, and related technology. Hate Speech, on the... more
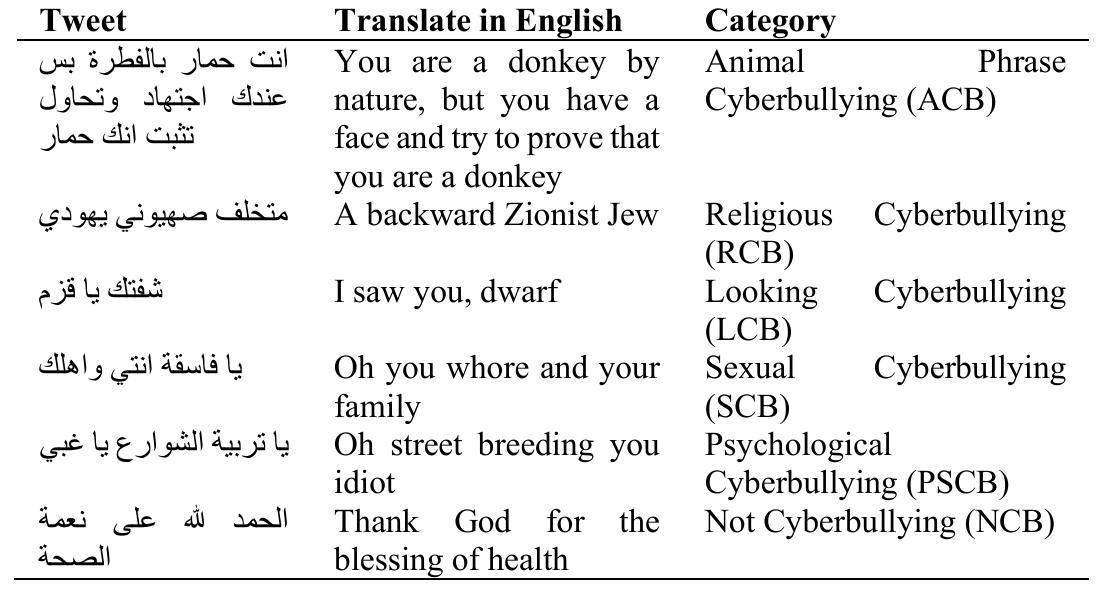
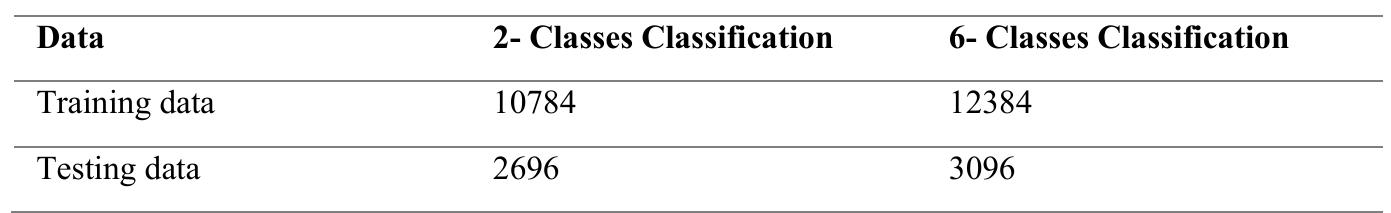
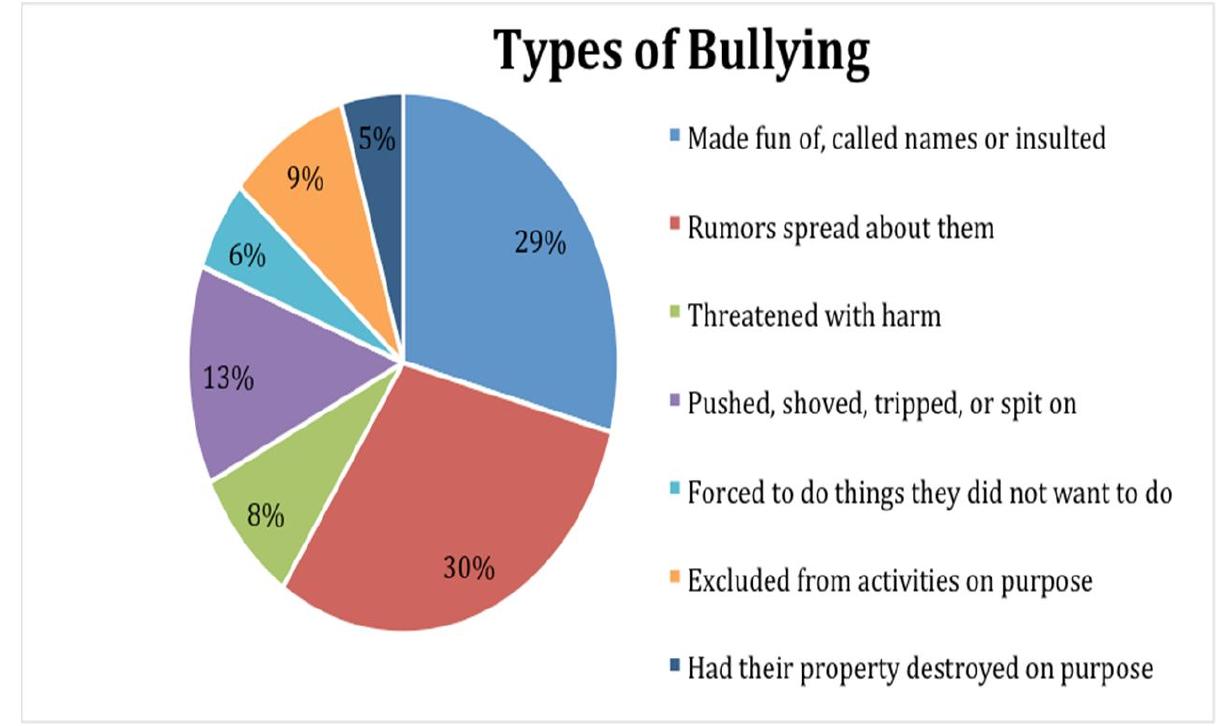
Abstract: Cyberbullying or cyber harassment is a form of bullying or harassment using electronic means. Cyberbullying and cyber harassment are also known as online bullying. It has become increasingly common, especially among teenagers,... more
Today, the internet is an integral part of our daily lives, enabling people to be more connected than ever before. However, this greater connectivity and access to information increase exposure to harmful content such as cyber-bullying... more
Half of the entire social media users in Indonesia has experienced cyberbullying. Cyberbullying is one of the treatments received as an attack with abusive words. An abusive word is a word or phrase that contained harassment and is... more
How well can hate speech concept be abstracted in order to inform automatic classification in codeswitched texts by machine learning classifiers? We explore different representations and empirically evaluate their predictiveness using... more
Akivaizdu, kad naudojimasis socialiniais tinklalapiais nuosekliai auga. Lietuvoje pastaraisiais metais vyksta spartus naudojimasis, įskaitant ir vietinius (nacionalinius) socialinius tinklus. "Facebook" yra tarp 10 labiausiai lankomų... more
Hate speech is a prevalent issue on social media platforms that has recently been a cause for concern due to its detrimental effects on individuals and society. The development of effective hate speech detection procedures and algorithms... more
Businesses are more concerned than ever about hate speech content as most brand communication and advertising move online. Different organisations may be incharge of their products and services but they do not have complete control over... more
Social media has shown to be a medium for the exchange of information, conducting commerce, and even for religious and political activity. The same site has been used to disseminate cyberbullying and hate speech. Cyberbullying is an... more
Interconnections between bacteria were more stable but less complex than interconnections between fungi along restoration of lowland forests.
Social media has shown to be a medium for the exchange of information, conducting commerce, and even for religious and political activity. The same site has been used to disseminate cyberbullying and hate speech. Cyberbullying is an... more
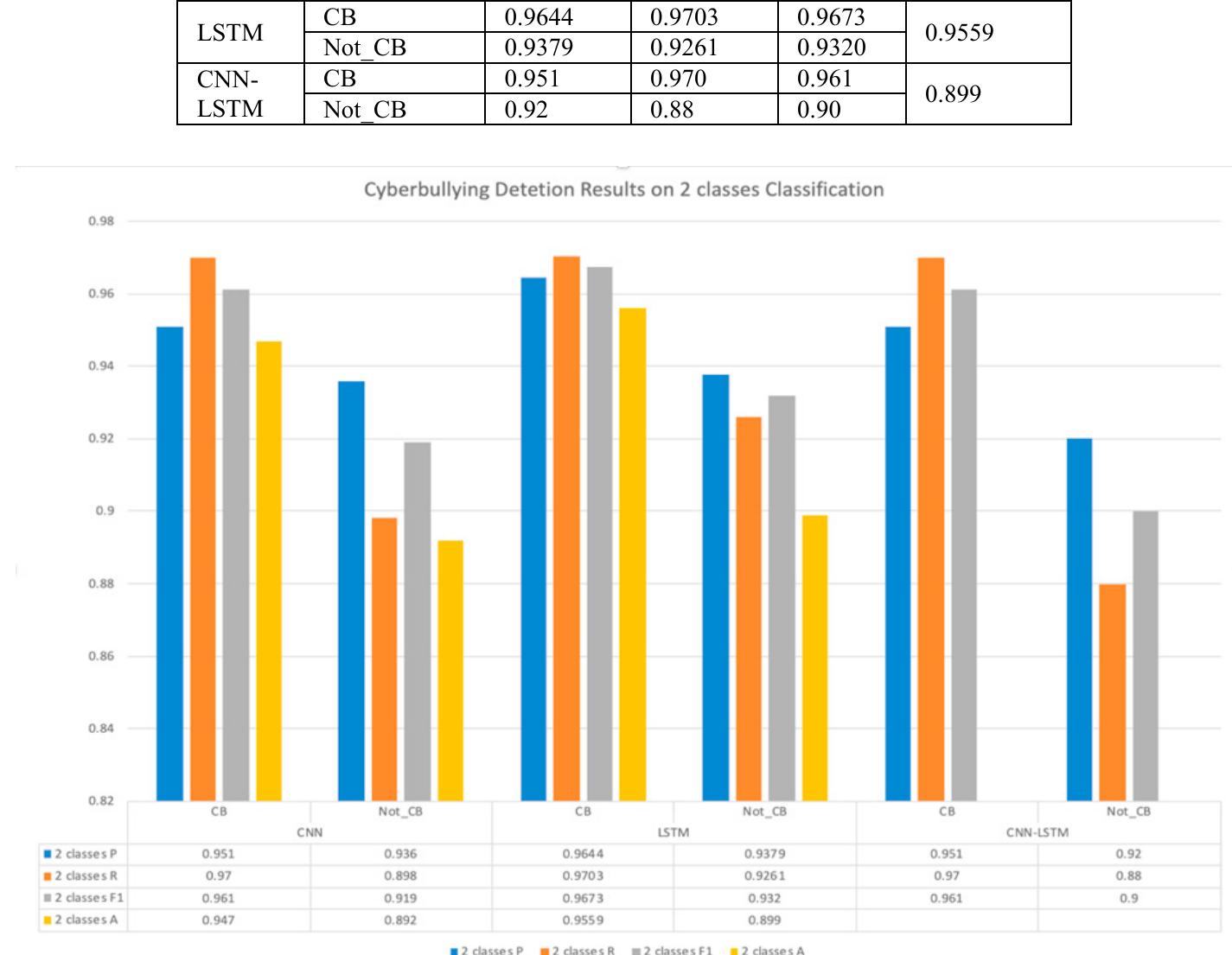
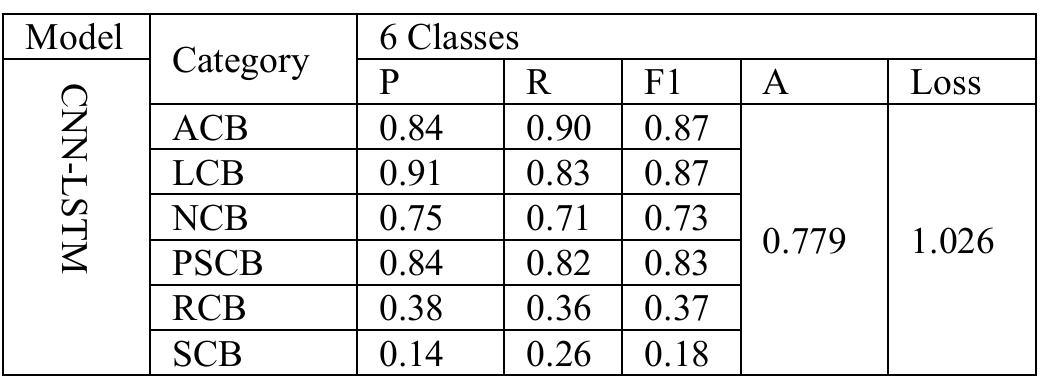
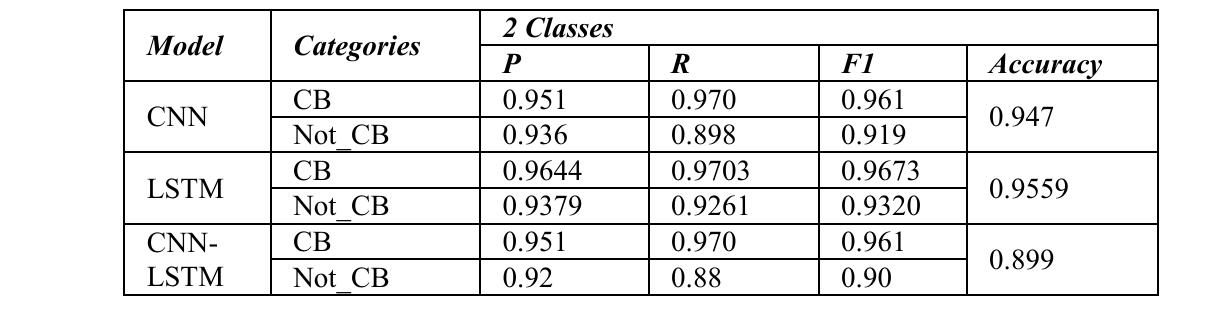
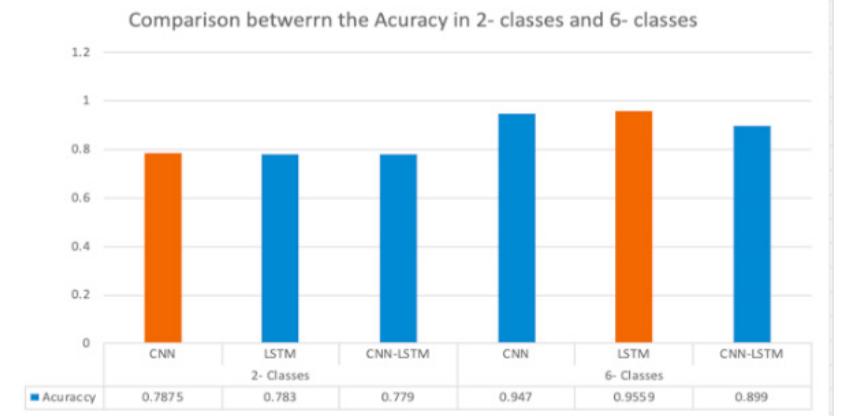
Cyberbullying (CB) is classified as one of the severe misconducts on social media. Many CB detection systems have been developed for many natural languages to face this phenomenon. However, Arabic is one of the under-resourced languages... more
Cyberbullying (CB) is classified as one of the severe misconducts on social media. Many CB detection systems have been developed for many natural languages to face this phenomenon. However, Arabic is one of the under-resourced languages... more
There has been a huge growth in recent years interest in studies on abusive language and cyberbullying detection due to its effects on both individual victims and societies. Hate speech, bullying, racism, aggressive content, harassment... more
This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY
Mining social web text has been at the heart of the Natural Language Processing and Data Mining research community in the last 15 years. Though most of the reported work is on widely spoken languages, such as English, the significance of... more
The use of social media has grown exponentially over time with the growth of the Internet and has become the most influential networking platform in the 21st century. However, the enhancement of social connectivity often creates negative... more
This paper describes SalamNET, an Arabic offensive language detection system that has been submitted to SemEval 2020 shared task 12: Multilingual Offensive Language Identification in Social Media. Our approach focuses on applying multiple... more
Businesses are more concerned than ever about hate speech content as most brand communication and advertising move online. Different organisations may be incharge of their products and services but they do not have complete control over... more
People crave interaction and connection with other people. Therefore, social media became the center of society's life. Among the brightest social media platforms nowadays with a massive number of daily users there is Instagram, which is... more
There is growing interest in automating crime detection and prevention for large populations as a result of the increased usage of social media for victimization and criminal activities. This area is frequently researched due to its... more
![TABLEI. SUMMARIZATION OF STUDY IN CYBERBULLYING DETECTION Based on [12], authors implemented binary classifier; Naive Bayes, Rule-based JRiP, Tree-based J48 ar Support Vector Machine (SVM). Two experiments were set up where first experiment used binary classifier | train three labels dataset (intelligence, culture &race and sexuality). Second experiment was integrated thre datasets into a single dataset and trained using multiclass. Result shows that binary classifier with three lab were better in terms of accuracy instead of using multiclass classifiers with one d Accuracy of rule-based JRip was better than other binary classifiers. In other studied by [13] and [14], they mentioned binary classifier (SVM) used ataset. as classification algorithm. E integrated BoW and polarity, result for F-scores was better than using single feature in SVM classification. On the other hand, [15] implemented linear SVM, logistic regression, decision tree and AdaBoost as classifier However, only linear SVM gave a better result instead of decision tree and Ad aBoost. Result of precision ar recall for both linear SVM and logistic regression were quite similar for cyberaggresion detection. Linear SVM was also used by [16] to learn featured. EBoW model showed precision and recall compared to BoW, sBow, LSA and LDA when implemented In summary, all of the studies used SVM as classification algorithm. Frequent that SVM is popular among others classifiers in supervised learning approach. better performance in terms | linear SVM as classifier. use SVM by researchers shov SVM is suitable for high-ske text classification such as to detect cyberbullying using content-based features 18]. Any circumstances such ; missing data, type of features and computer performance, SVM still outperform other classifiers [17]. Table shows the summarization of data source, features used and classification in c research works as discussed. yberbullying detection for eac](https://figures.academia-assets.com/114489938/table_001.jpg)
![Table 3. Shows the recall, precision, and Fl-measure scores for four classifiers on two tests [17] 5. CONCLUSION](https://figures.academia-assets.com/107246652/table_002.jpg)

![Figure 1. Framework for Arabic fake news detection In this study, the authors suggested a method for detecting cyberbullying that employs AI-basec classifiers and language-independent characteristics. In light of this, our method may be used to train and classify articles written in any language. The technique is based on “long short term memory (LSTM)’ “CNN*. bidirectional long short-term memory (Bi-LSTM), and gated recurrent unit (GRU) models that have been trained using data from a distributed feature space [17], such as word or character embedding. We’ll describe the various steps we took to create our cyberbullying detection algorithm and the rationale behind each one. At the same time, evaluate the results of the investigations and compare them to those in the academic literature. As shown in the Figure | explain the steps of the methodology of our proposed methods.](https://figures.academia-assets.com/107246652/figure_001.jpg)
![3.2. Feature extraction technique is to reduce words to their stems [28]. An english token’s stem is produced by removing all of its suffixes; for instance, “connected, connecting, connection, connections” all become “connect,” as shown by [29]. Table | explains all of the document pre-processing procedures that were taken. The feature extraction procedure is critical for selecting the best feature set method. The authors employed t he ( Keras tokenizer) in this experiment. Keras tokenizers are classified as follows: This class enables the processing of a text corpus by converting each text into either a vector with a coefficient for each token that can be binary depending on word count, based on term frequency inverse document frequency (TF-IDF), or a sequence 0 integers, each of which represents the index of a token in a dictionary. Machine learning classifiers will be applied to the dataset in this project to improve accuracy utilizing a range of text feature selection techniques. dataset is d combined to o isp The TF and TF-IDF can be used to obtain text characteristics. The frequency of each word in the ayed by the TF. In addition to weighing each word in the dataset, the TF and TF-IDF were btain the inverse document frequency [30]. His is a key stage in document categorization that improves a text classifier’s scalability, efficiency, and accuracy [31]. As a result, after pre-processing the text of documents, the properties are acquired from them.](https://figures.academia-assets.com/107246652/table_001.jpg)