Abstract: Current data mining tools are characterized by a plethora of algorithms but a lack of guidelines to select the right method according to the nature of the problem under analysis. Producing such guidelines is a primary goal by... more
In streaming data pipelines, append-only tables often accumulate duplicate records when ingestion occurs through Kafka and Dataflow into BigQuery. SQL views with window functions are commonly used to retrieve the latest record per primary... more
Abstract: The management of engineering assets such as facilities and equipments can be a challenging task and optimising their usage is critical. To ensure effective utilization of an asset, one has to make effective decisions regarding... more
The mobile office devices market is currently growing, mainly due to the descending cost of wireless technology as well as the high diversity of functions and features covered. Diversity and proliferation become a hard problem when a... more
Todos os direitos reservados e protegidos. Nenhuma parte destes anais poderá ser reproduzida ou transmitida sejam quais forem os meios empregados sem prévia autorização dos editores.
This work presents an XML-based authoring methodology that facilitates the different tasks associated with the development of standards-compliant e-learning content development. The idea is to support a unified authoring process of... more
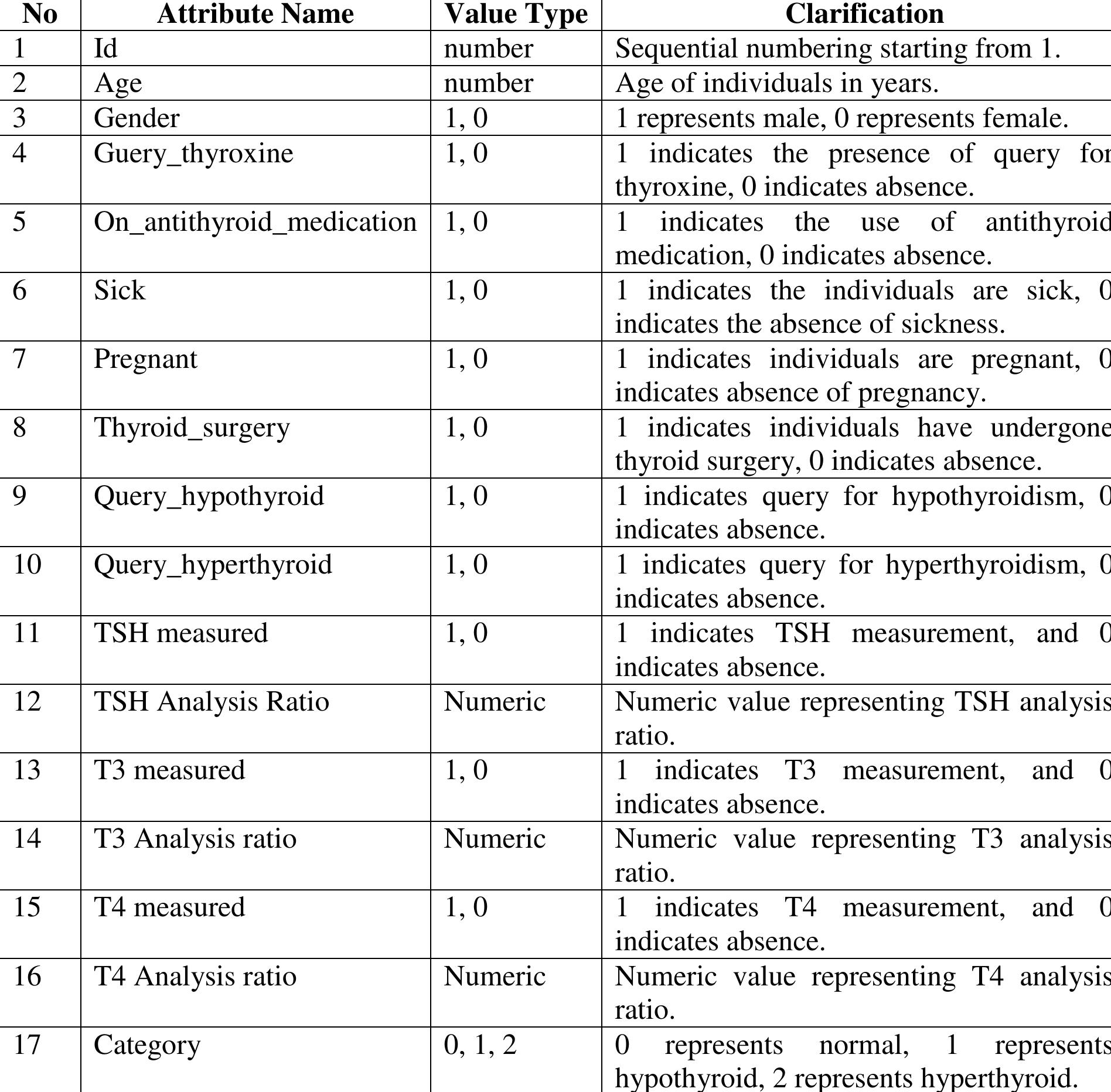
In recent years, thyroid diseases have become increasingly prevalent worldwide. In India, for instance, one in eight women is affected by hypothyroidism, hyperthyroidism, or thyroid cancer. Research indicates that approximately 20% of... more
A Markov chain is stochastic process with property that given the values of the process from time zero up through the current time, and one of its important applications is to model some evolutionary algorithms and to analyze their... more
It is an important and a complicated task to investigate the convergence of a new genetic algorithm based on quantum mechanics concepts including qubits and superposition of states, namely Quantum Genetic Algorithm, in the field of... more
The IMS Content Packaging Specification is a format that facilitates the deployment of discrete units of learning resources based on an XML structure called a manifest. The contents and structure of a content package are determined at... more
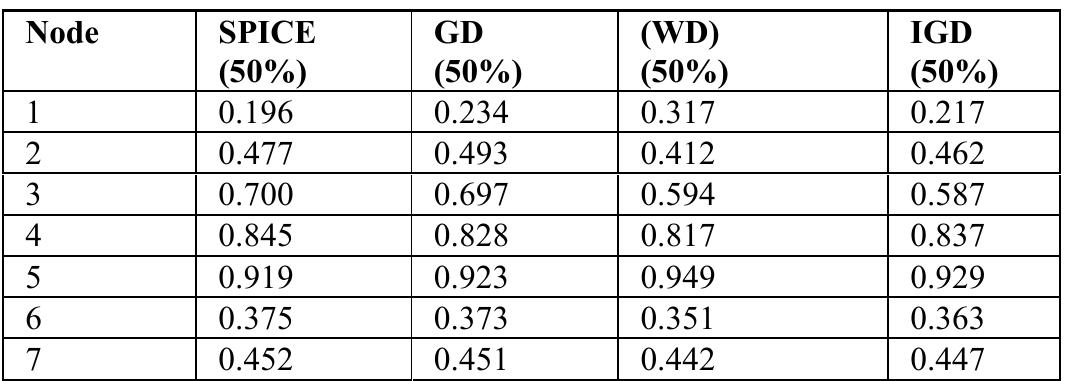
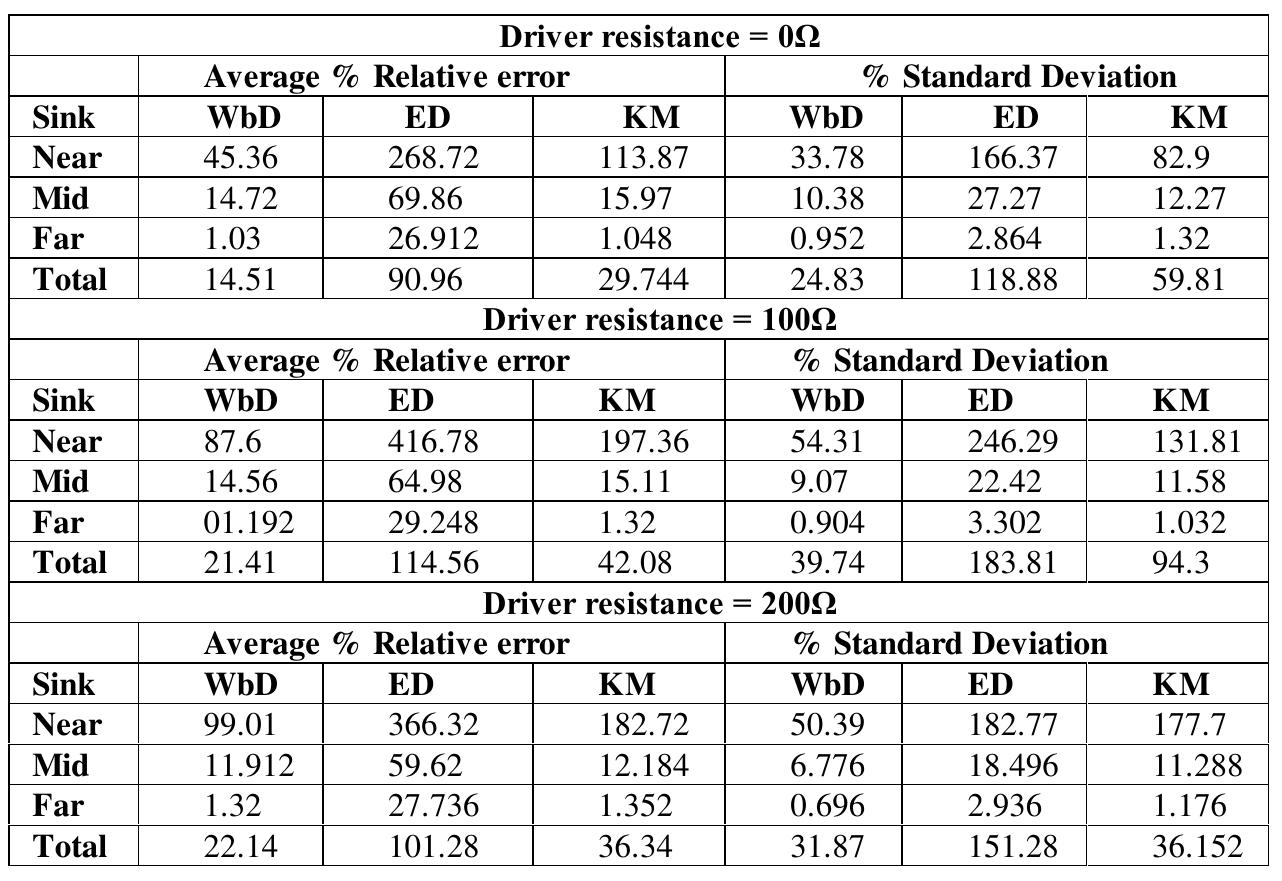
In this paper, we present an efficient model for onchip interconnects delay analysis. Several approaches have already been proposed for approximating the interconnect delay accurately and efficiently. Moments of the impulse response are... more
It is an important and a complicated task to investigate the convergence of a new genetic algorithm based on quantum mechanics concepts including qubits and superposition of states, namely Quantum Genetic Algorithm, in the field of... more
It is an important and a complicated task to investigate the convergence of a new genetic algorithm based on quantum mechanics concepts including qubits and superposition of states, namely Quantum Genetic Algorithm, in the field of... more
Component-based software engineering is widely expected to revolutionize the way in which software systems are developed and maintained. However, companies who wish to adopt the component paradigm for serious enterprise software... more
Component-based software engineering is widely expected to revolutionize the way in which software systems are developed and maintained. However, companies who wish to adopt the component paradigm for serious enterprise software... more
International Journal of Computer science & Information Technology (IJCSIT), Vol 1, No 2, November 2009 ... Hazra Imran 1 and Aditi Sharan 2 ... 1 Department of Computer Science, Jamia Hamdard ,New Delhi ,India [email protected]... more
Authoring context-based adaptive m-learning environments, in which both individual and collaborative activities can be adaptively proposed to each user according to his/her context, is not an easy task. In order to recommend the most... more
Chronic stress is a significant contributor to emotional distress and a myriad of health issues. Some coping mechanisms for stress and anxiety often have significant barriers preventing people from seeking a remedy. A new home-based... more
The main goal of this paper is to examine the fine granularity of learning content and its impact of the adaptability process in Adaptive Learning Systems (ALS). For that purpose, we present the concept and the essence of learning... more
Digital image processing is one of the emerging technologies in present economically and technologically developing world. Generally image processing includes importing the image with optical scanner or by digital photography, then... more
In high speed digital integrated circuits, interconnects delay can be significant and should be included for accurate analysis. Delay analysis for interconnect has been done widely by using moments of the impulse response, from the... more
iStarML is an XML-based format for enabling interoperability among i* tools. Its main design focus was to support data interchange even when involved tools implement different i* variants. In this paper we analyse required changes to the... more
In the lifelong learning context, the efficiency of learning is measured according to the users' achievement of the target competences. However, in a virtual learning environment supporting the competence development process ends up being... more
Image retrieval has been one of the most interesting and vivid research areas in the field of computer vision over the last decades. Content Based Image Retrieval (CBIR) basically is a technique to perform retrieval of the images from a... more
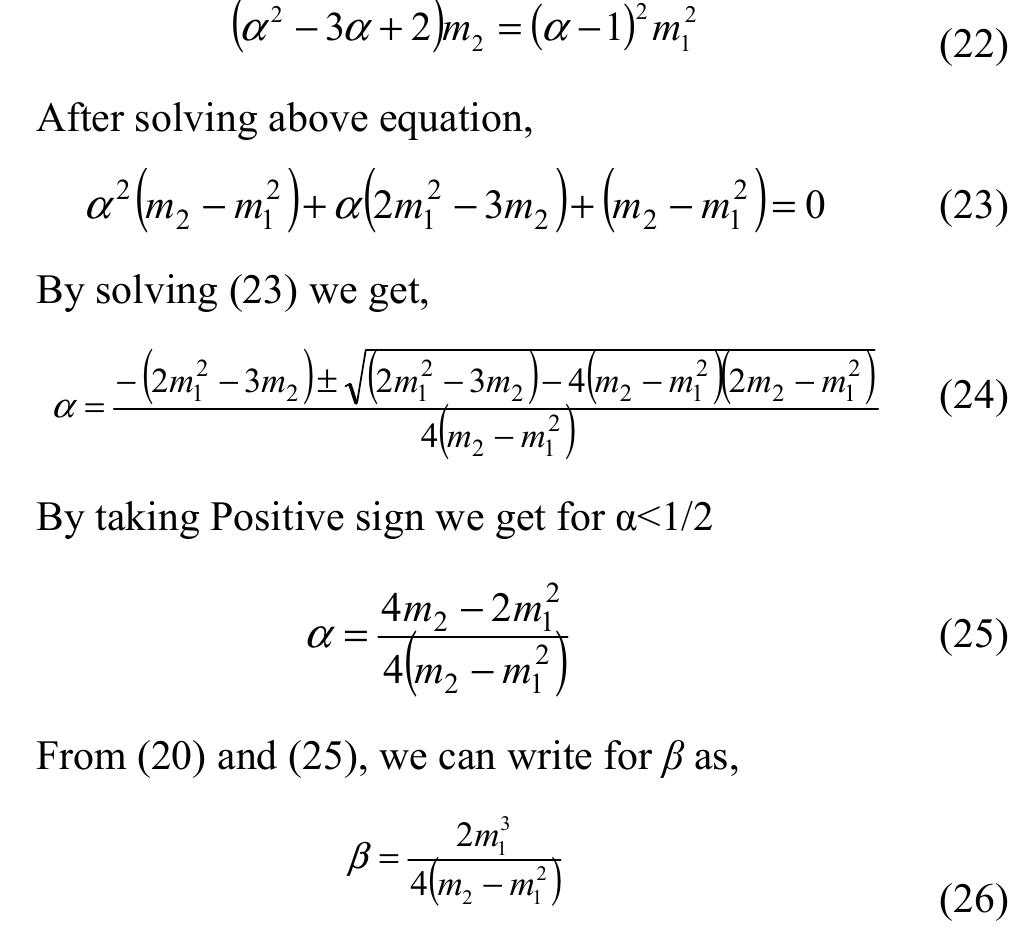
This work presents an accurate and efficient model to compute the delay and slew metric of on-chip interconnect of high speed CMOS circuits foe ramp input. Our metric assumption is based on the Burr's Distribution function. The Burr's... more
In deep sub-micrometer (DSM) regime the on-chip interconnect delay is significantly more dominating than the gate delay. Several approaches have been proposed to capture the interconnect delay accurately and efficiently. By interpreting... more
As technology scales down, timing verification of digital integrated circuits becomes an extremely difficult task due to statistical variations in the gate and wire delays. Statistical timing analysis techniques are being developed to... more
Moments of the impulse response are widely used for interconnect delay analysis, from the explicit Elmore delay (the first moment of the impulse response) expression, to moment matching methods which creates reduced order trans-impedance... more
This paper presents how the learning objects are deployed in learning support environment. The design of content packages are described in the proposed model by integrating learning technology standards, specifications and instructional... more
Component-based software engineering is widely expected to revolutionize the way in which software systems are developed and maintained. However, companies who wish to adopt the component paradigm for serious enterprise software... more
Component-based software engineering is widely expected to revolutionize the way in which software systems are developed and maintained. However, companies who wish to adopt the component paradigm for serious enterprise software... more
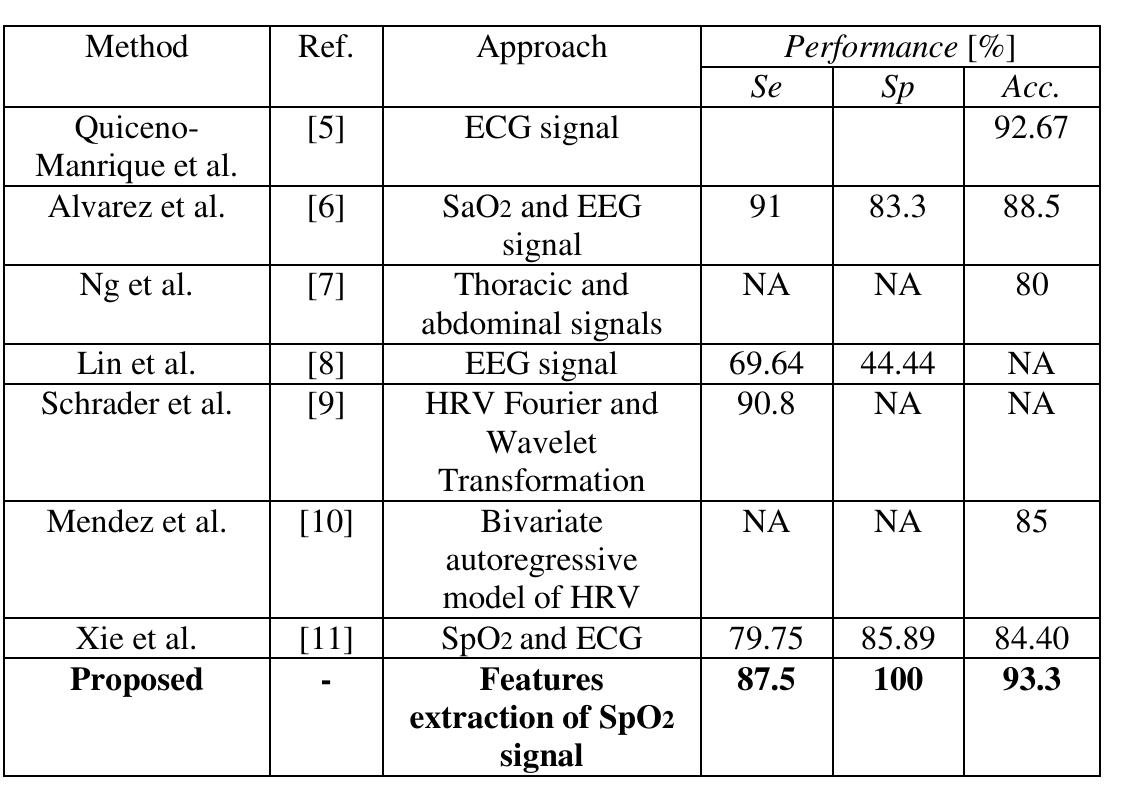
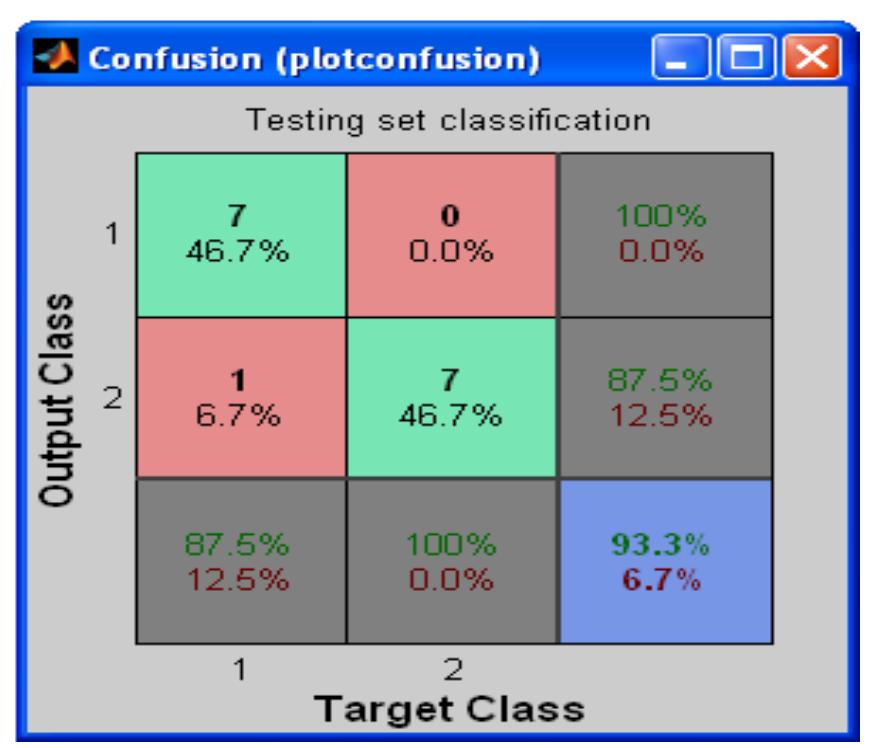
Obstructive sleep apnea (OSA) is a common disorder in which individuals stop breathing during their sleep. These episodes last 10 seconds or more and cause oxygen levels in the blood to drop. Most of sleep apnea cases are currently... more
DARPA sponsored the first realistic and systematic evaluation of research intrusion detection systems in 1998. As part of this evaluation, MIT Lincoln Laboratory developed a test network which simulated a medium-size government site.... more
The problem of closed-loop enhanced sensitivity design is as follows: given a linear, timeinvariant system, find a (realizable) feedback gain such that (1) the closed-loop is stable in the reference and the potentially damaged states, and... more
In this paper, authors evaluate machine learning algorithms to detect the trustworthiness of a website according to HONcode criteria of conduct (detailed in paper). To derive a baseline, we evaluated a Naive Bayes algorithm, using single... more
This paper presents an approach to model content based metasearch engine which search all the content related images present in the dataset. Searching through the keywords in an image database require a lot of Meta data (keywords about... more
With recent technological growth, use of mobile devices is also increased, every one having smart phone with them and now days it became one of the necessary thing. Visual Search has become recent trend in fields like information... more
Wireless Sensor Networks are becoming one of the most successful choices for the development and deployment of applications in a range of scenarios, from intelligent homes to environment monitoring. Nowadays, there is a growing demand for... more
In this article we present a 2D cellular automaton (Class_AC) to solve a problem of text mining in the case of unsupervised classification (clustering). Before to experiment the cellular automaton, we vectorized our data indexing textual... more
Authoring context-based adaptive m-learning environments, in which both individual and collaborative activities can be adaptively proposed to each user according to his/her context, is not an easy task. In order to recommend the most... more
Authoring context-based adaptive m-learning environments, in which both individual and collaborative activities can be adaptively proposed to each user according to his/her context, is not an easy task. In order to recommend the most... more
Abstract: In this paper, a few novel data hiding techniques are proposed. These techniques are improvements over the classical LSB data hiding technique and the Fibonacci LSB data-hiding technique proposed by Battisti et al.\ cite {r1}.... more
The goal of personalized search is to provide user with results that accurately satisfy their specific goal of the search. In this paper, a hybrid personalized search re-ranking approach is proposed to provide users with results reordered... more
Intrusion detection systems (IDS) have become an essential issue for computer networks security since each one is vulnerable for violation. This paper presents a neural network based implementation of an intrusion detection system to... more
Testing is an important part of quality assurance in the software development life cycle. As the complexity and size of software grow, more and more time and man power are required for testing the software. Manual testing is very much... more
This paper presents how the learning objects are deployed in learning support environment. The design of content packages are described in the proposed model by integrating learning technology standards, specifications and instructional... more
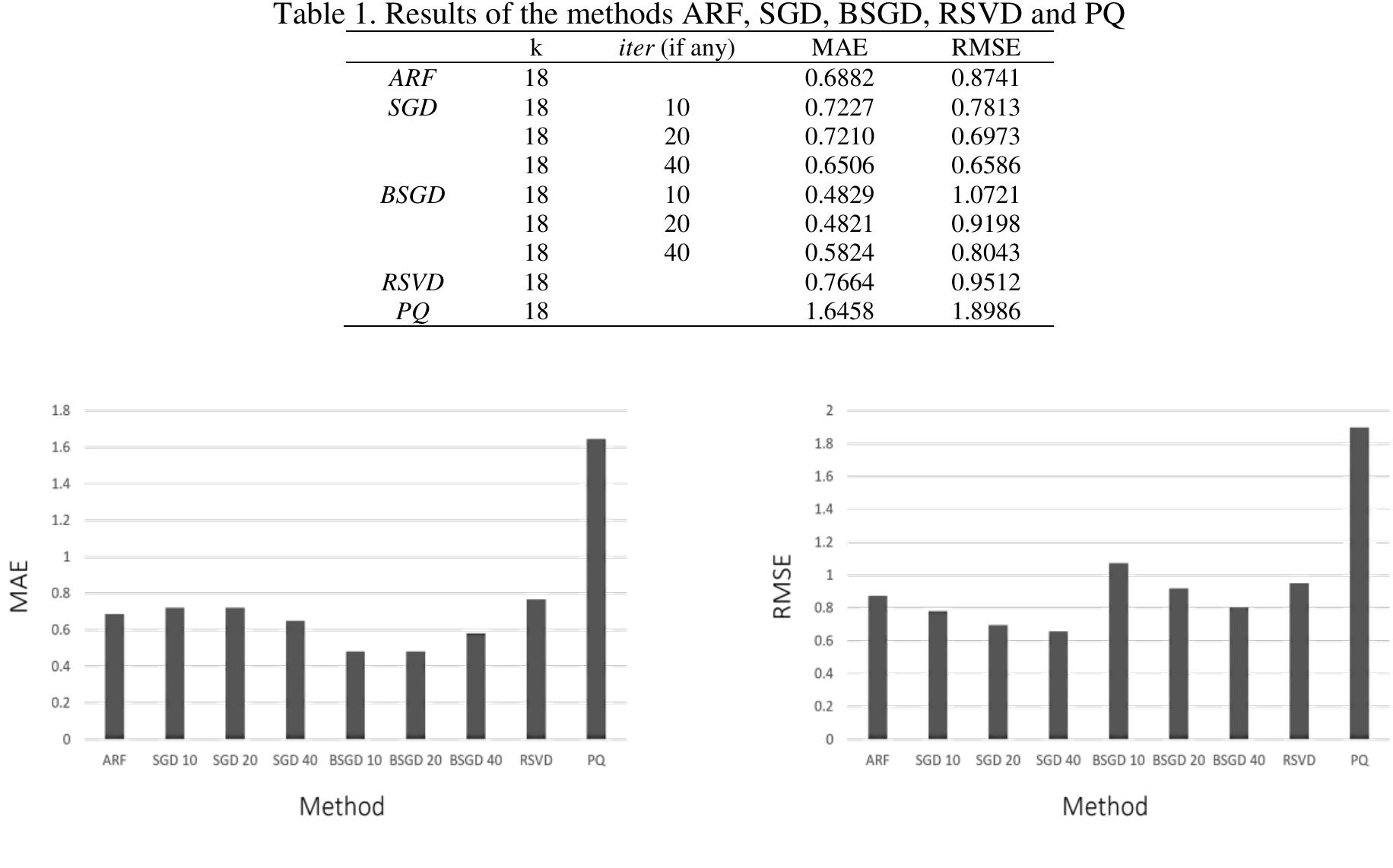
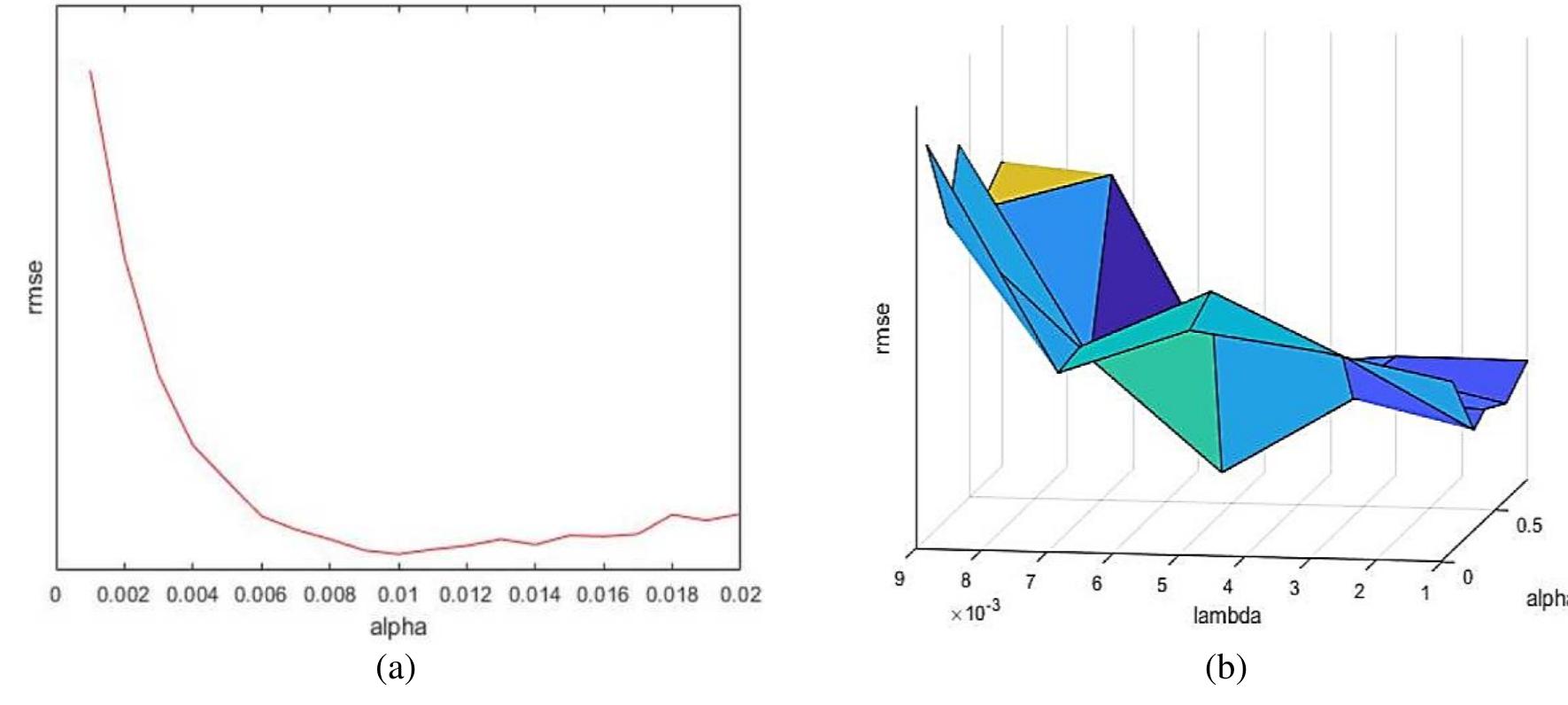
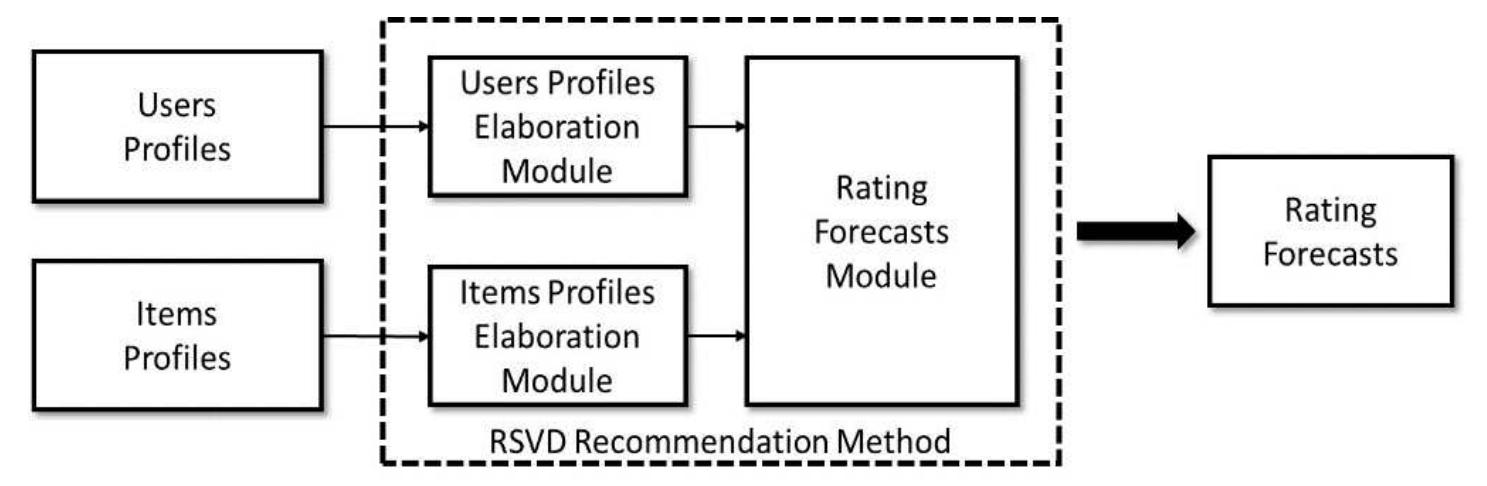
Due to modern information and communication technologies (ICT), it is increasingly easier to exchange data and have new services available through the internet. However, the amount of data and services available increases the difficulty... more
In this paper, we are presenting a new approach for gender & age determination based on image mining with C means clustering. Image Mining is an area which is used for pattern recognition & other application.
abstract={The workshop on Usage Analysis and the Web of Data (USEWOD2011) was the first workshop in the field to investigate combinations of usage data with semantics and the Web of Data. Questions the workshop aims to address are for... more
It is an important and a complicated task to investigate the convergence of a new genetic algorithm based on quantum mechanics concepts including qubits and superposition of states, namely Quantum Genetic Algorithm, in the field of... more
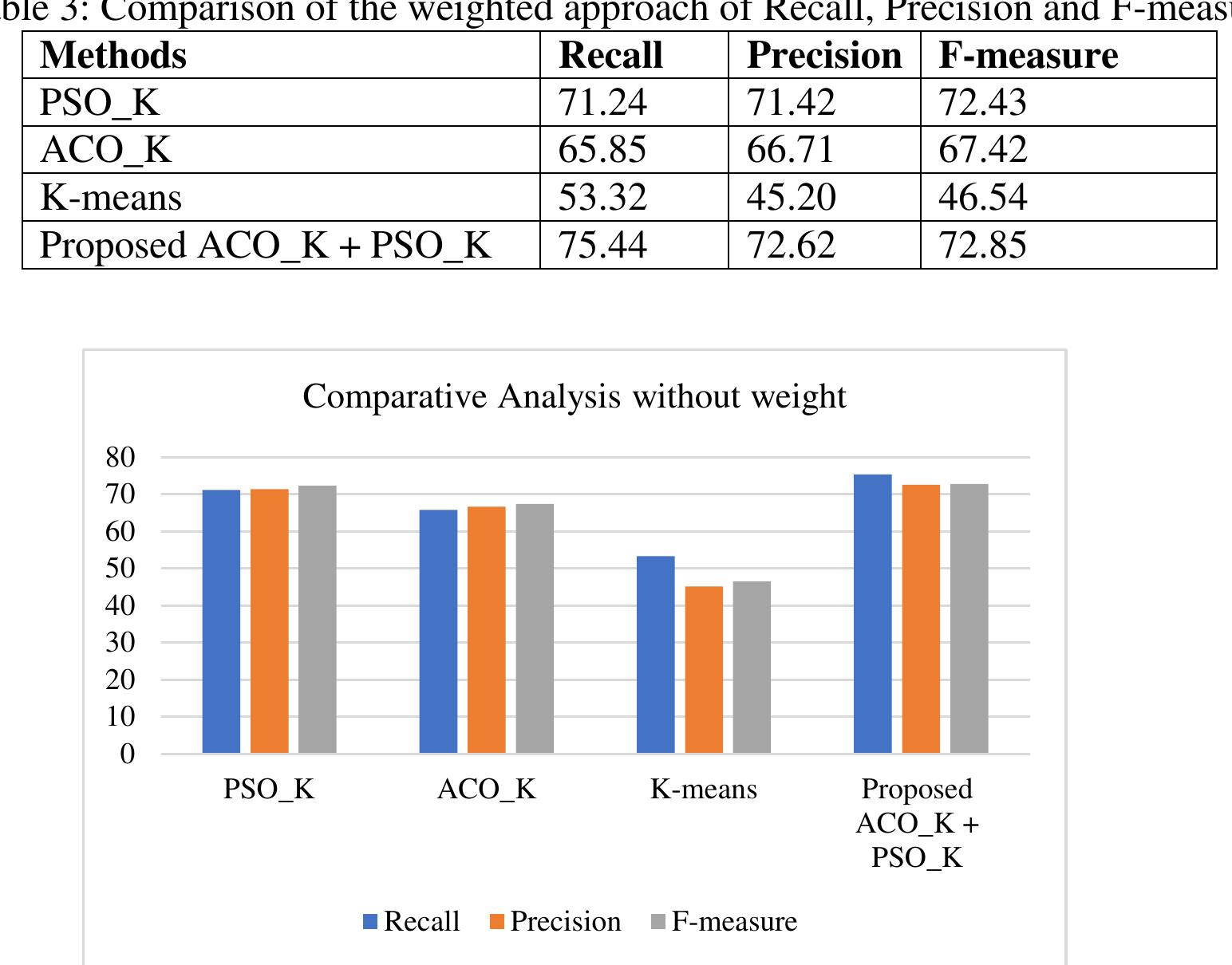
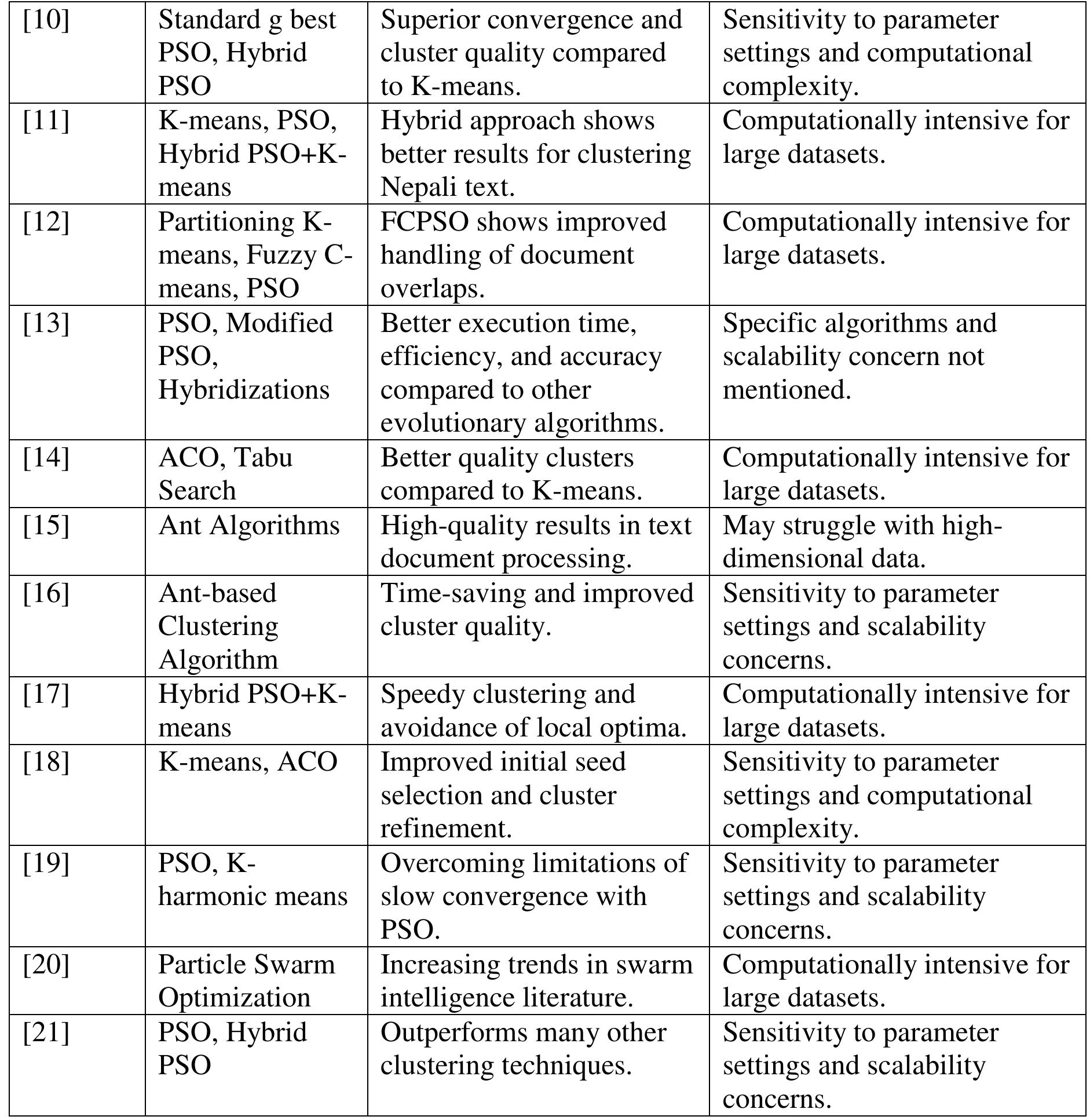
![The literature review encompasses various methodologies and algorithms applied in web document clustering and information retrieval. One notable contribution is the Vector Space Model, which utilizes Term Frequency-Inverse Document Frequency weighting schemes for text document representation. Furthermore, genetic algorithms have been explored to optimize HTML tag weights, shedding light on the importance of anchor and header tags in improving retrieval performance [17-18]. Document clustering emerges as a crucial tool for efficient information access, particularly in facilitating rapid access to relevant content through localized clustering. While traditional clustering algorithms like K-means have been foundational, their limitations have spurred the integration of optimization techniques such as Particle Swarm Optimization (PSO) and Ant Colony Optimization (ACO) [19-20]. Overall, the literature underscores a dynamic landscape, with a growing focus on hybrid methodologies that amalgamate meta-heuristic optimization with traditional clustering techniques to enhance information retrieval efficiency.](https://figures.academia-assets.com/117922502/table_001.jpg)
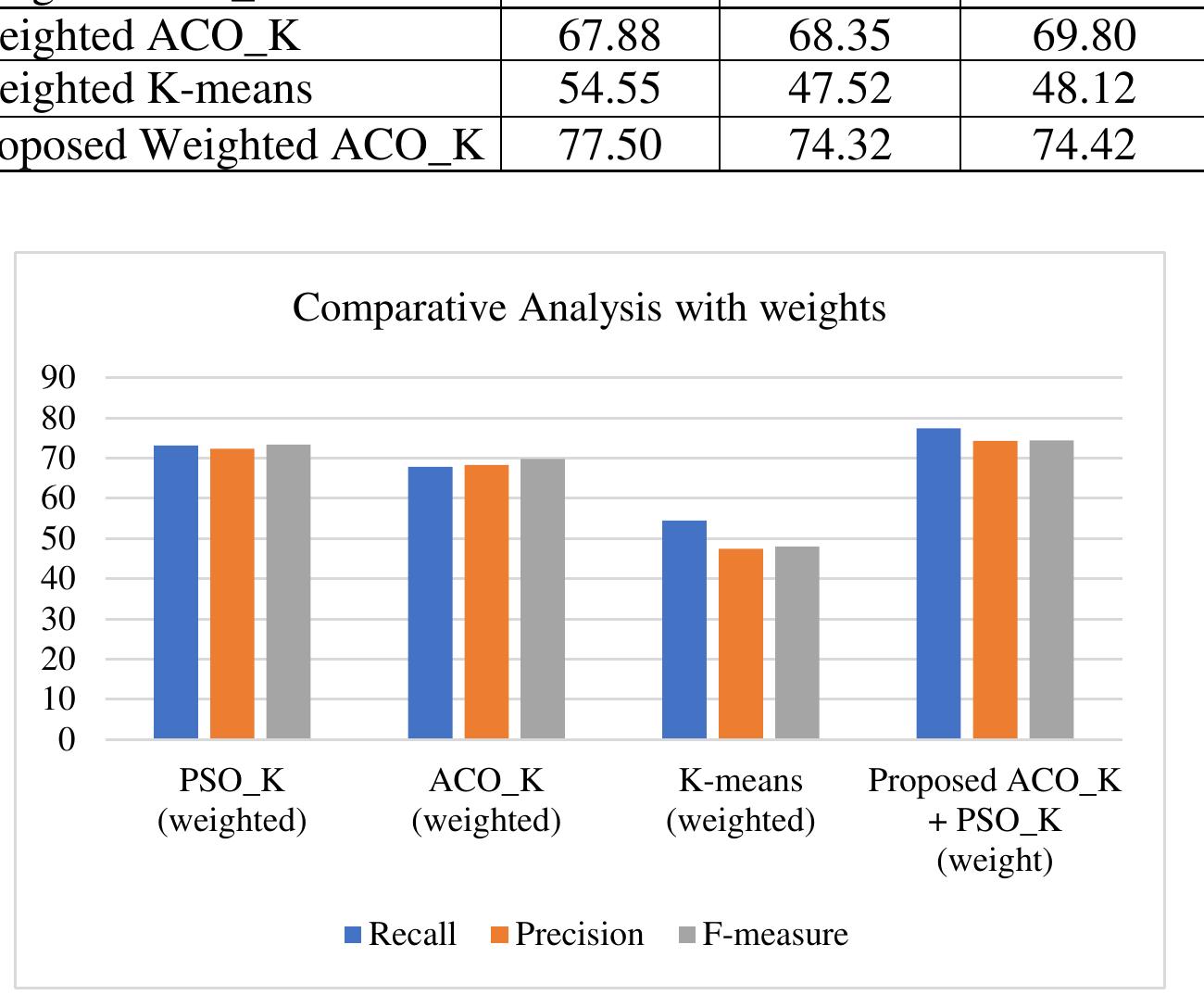
![Table 4 presents a comparative analysis of various classification models and _ their corresponding accuracies derived from different studies. Each study utilized distinct classification techniques to analyze and classify thyroid diseases. K-nearest neighbour (KNN) emerges with the highest accuracy of 73.44% in Study [25], followed closely by the J48 decision tree with 69.58% accuracy in Study [26]. Decision tree models, as seen in Studies [27] and [28], achieve accuracies of 68.89% and 69.00%, respectively. Logistic regression in Study [29] yields an accuracy of 67.81%, while Random Forest and Naive Bayes methods in Studies [30] and [31] achieve accuracies of 65.51% and 67.36%, respectively. Decision Trees in the Study [32] attain an accuracy of 64.62%. Intriguingly, the proposed models, ACO_K + PSO (weighted) and ACO_K + PSO_K, exhibit notably higher accuracies of 77.50% and 75.44% respectively, showcasing their potential superiority in thyroid disease classification. These results underscore the effectiveness of the proposed hybrid models in accurately classifying thyroid diseases compared to traditional classification techniques.](https://figures.academia-assets.com/117922502/table_004.jpg)
![We compared the delays obtained from SPICE, Weibull Distribution (WD) [11] and Gamma Distribution (GD) [12] with those found using the inverse gamma approximation (IGD). The results for the 50% delay are summarized in Table I. and applied it to widely used actual interconnect RC networks as shown in Fig. 1. For each RC network source we place a driver, where the driver is a voltage source followed by a resister.](https://figures.academia-assets.com/112525980/figure_002.jpg)
![according to how well a person is breathing and how well the blood is being pumped around the body [13].](https://figures.academia-assets.com/102296355/figure_002.jpg)
![In the training phase, the Purelin linear transfer function has been used as an activation function of the output layer of the network (for improving error derivative) [18]. Since the output space must be divided into two regions: OSA positive and OSA negative, we suggest using a single output node.](https://figures.academia-assets.com/102296355/figure_005.jpg)
![Figure 1. SpO2 record with OSA negative subject [12]. SpO, is the amount of oxygen being carried by the red blood cell in the blood. Very simply, SpO, goes up and down](https://figures.academia-assets.com/102296355/figure_001.jpg)
![Central tendency measure with radius 0.5 (CTMS50): This measure applied in [16]. CTM50 is computed by selecting a circular region of radius 0.5 around the origin, counting the number of points that fall within the radius, and dividing by the total number of points. Given N data points from a time series, N-2 would be the total number of points in the scatter plot. Hence, CTMS0 can be computed as [17]:](https://figures.academia-assets.com/102296355/figure_003.jpg)