説明
2要素認証プラグインは、パスワードに加えて別の認証方法をユーザーに要求することで、WordPress のログインにセキュリティの層を追加します。これにより、パスワードが漏洩した場合でも、不正アクセスから保護できます。
セットアップ手順
Important: Each user must individually configure their two-factor authentication settings.
For Individual Users
- Navigate to your profile: Go to “Users” “Your Profile” in the WordPress admin
- Find Two-Factor Options: Scroll down to the “Two-Factor Options” section
- Choose your methods: Enable one or more authentication providers (noting a site admin may have hidden one or more so what is available could vary):
- Authenticator App (TOTP) – Use apps like Google Authenticator, Authy, or 1Password
- メールコード – Receive one-time codes via email
- Backup Codes – Generate one-time backup codes for emergencies
- ダミーメソッド – For testing purposes only (requires WP_DEBUG)
- Configure each method: Follow the setup instructions for each enabled provider
- Set primary method: Choose which method to use as your default authentication
- Save changes: Click “Update Profile” to save your settings
For Site Administrators
- Plugin settings: The plugin provides a settings page under “Settings Two-Factor” to configure which providers should be disabled site-wide.
- User management: Administrators can configure 2FA for other users by editing their profiles
- Security recommendations: Encourage users to enable backup methods to prevent account lockouts
Available Authentication Methods
Authenticator App (TOTP) – Recommended
- セキュリティ: 高 – 時間ベースのワンタイムパスワード
- Setup: Scan QR code with authenticator app
- Compatibility: Works with Google Authenticator, Authy, 1Password, and other TOTP apps
- Best for: Most users, provides excellent security with good usability
リカバリーコード – 推奨
- セキュリティ: 中 – 一度だけ使用するコード
- Setup: Generate 10 backup codes for emergency access
- Compatibility: Works everywhere, no special hardware needed
- Best for: Emergency access when other methods are unavailable
メールコード
- セキュリティ: 中 – メールで送信されるワンタイムコード
- Setup: Automatic – uses your WordPress email address
- Compatibility: Works with any email-capable device
- Best for: Users who prefer email-based authentication
FIDO U2F 秘密鍵
- Deprecated and removed due to loss of browser support.
ダミーメソッド
- セキュリティ: なし – 常に成功
- Setup: Only available when WP_DEBUG is enabled
- Purpose: Testing and development only
- Best for: Developers testing the plugin
重要な注意事項
HTTPS Requirement
- All methods work on both HTTP and HTTPS sites
ブラウザーの互換性
- TOTP and email methods work on all devices and browsers
アカウント復元
- Always enable backup codes to prevent being locked out of your account
- すべての認証方法にアクセスできなくなった場合は、サイト管理者に連絡してください。
セキュリティのベストプラクティス
- 可能な場合は複数の認証方法を使用する
- バックアップしたコードを安全な場所に保管する
- Regularly review and update your authentication settings
For more information about two-factor authentication in WordPress, see the WordPress Advanced Administration Security Guide.
詳細な経緯は、この記事を参照してください。
アクション & フィルター
プラグインで提供するアクションフックとフィルターフックは以下のとおり:
two_factor_providersフィルターフックは、メールや Time Based One-Time Password などの利用可能な2要素認証プロバイダーを上書きします。配列値は、二要素認証プロバイダーの PHP クラス名です。two_factor_providers_for_userフィルターは、特定のユーザーが利用可能な二要素認証プロバイダーを上書きします。配列の値はプロバイダークラスのインスタンスで、2番目の引数にはユーザーオブジェクトWP_Userを指定します。two_factor_enabled_providers_for_userフィルターフックは、ユーザーに対して有効化している二要素認証プロバイダーの一覧を上書きします。最初の引数は、有効なプロバイダークラス名の配列であり、2番目の引数はユーザーIDです。two_factor_user_authenticatedアクションフックは、認証処理直後に、ログインしたユーザーを判別するための最初の引数として、ログインしたWP_Userオブジェクトを返します。two_factor_user_api_login_enableフィルターは REST API と XML-RPC での認証をアプリケーションパスワードのみに制限します。2番目の引数にユーザー ID が提供されます。two_factor_email_token_ttlフィルターフックは、メールトークン生成後の有効期間を秒単位で上書きします。第一引数として秒単位の時間を受け付け、また、認証するWP_Userオブジェクトの ID も受け付けます。two_factor_email_token_lengthフィルターは、メールトークンのデフォルト文字数8を上書きします。two_factor_backup_code_lengthフィルターは、バックアップコードのデフォルトの文字数「8」を上書きします。関連付けられているユーザーのWP_Userを2番目の引数として指定します。two_factor_rest_api_can_edit_userフィルターは、REST API を介してユーザーの2要素認証の設定を編集できるかどうかを上書きします。1番目の引数は現在の$can_edit(真偽値)、2番目の引数はユーザー ID です。two_factor_before_authentication_promptaction which receives the provider object and fires prior to the prompt shown on the authentication input form.two_factor_after_authentication_promptaction which receives the provider object and fires after the prompt shown on the authentication input form.two_factor_after_authentication_inputaction which receives the provider object and fires after the input shown on the authentication input form (if form contains no input, action fires immediately aftertwo_factor_after_authentication_prompt).two_factor_login_backup_linksfilters the backup links displayed on the two-factor login form.
Redirect After the Two-Factor Challenge
To redirect users to a specific URL after completing the two-factor challenge, use WordPress Core built-in login_redirect filter. The filter works the same way as in a standard WordPress login flow:
add_filter( 'login_redirect', function( $redirect_to, $requested_redirect_to, $user ) {
return home_url( '/dashboard/' );
}, 10, 3 );
スクリーンショット
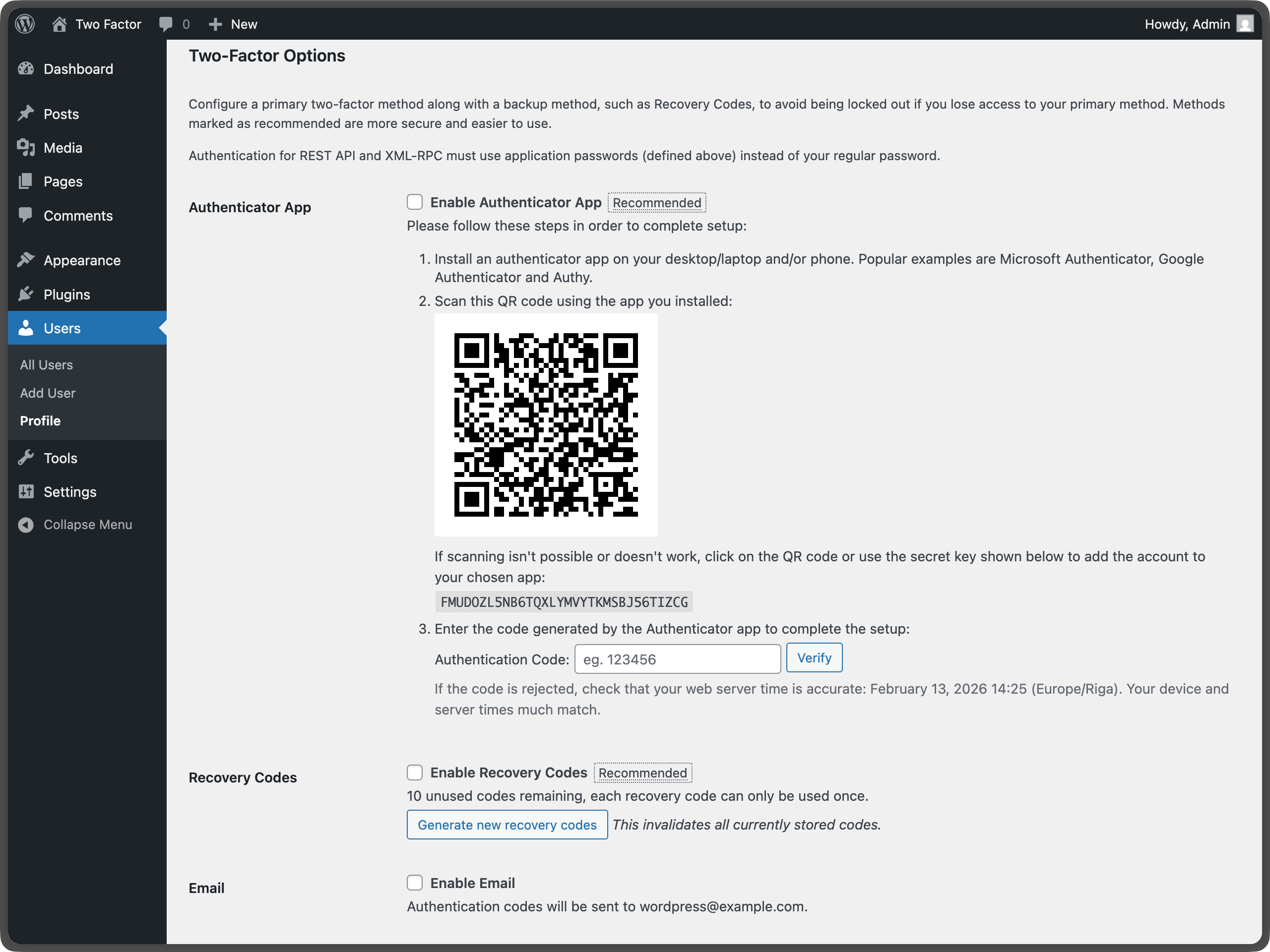
Two-factor options under User Profile – Shows the main configuration area where users can enable different authentication methods. 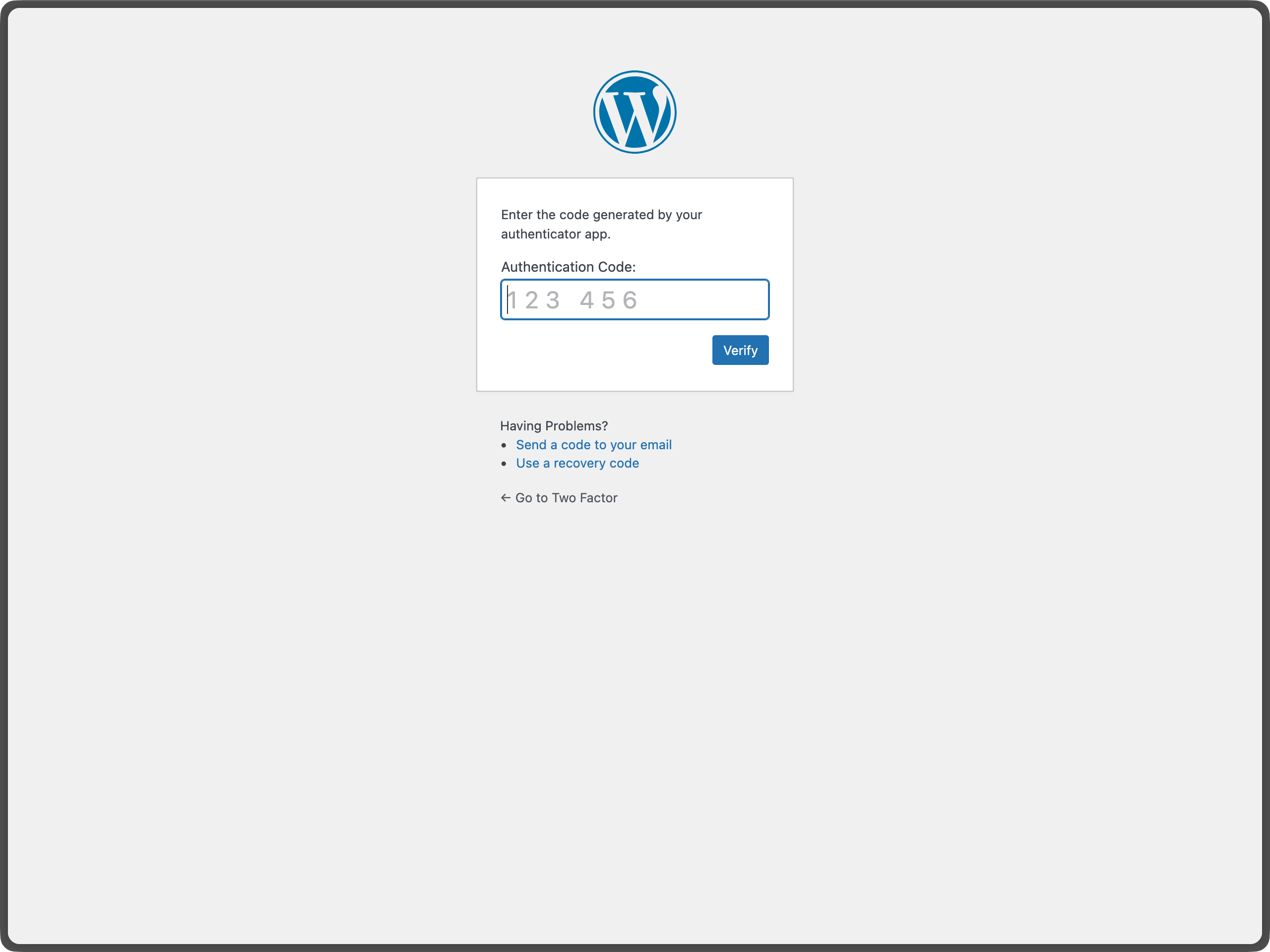
Email Code Authentication during WordPress Login – Shows the email verification screen that appears during login. 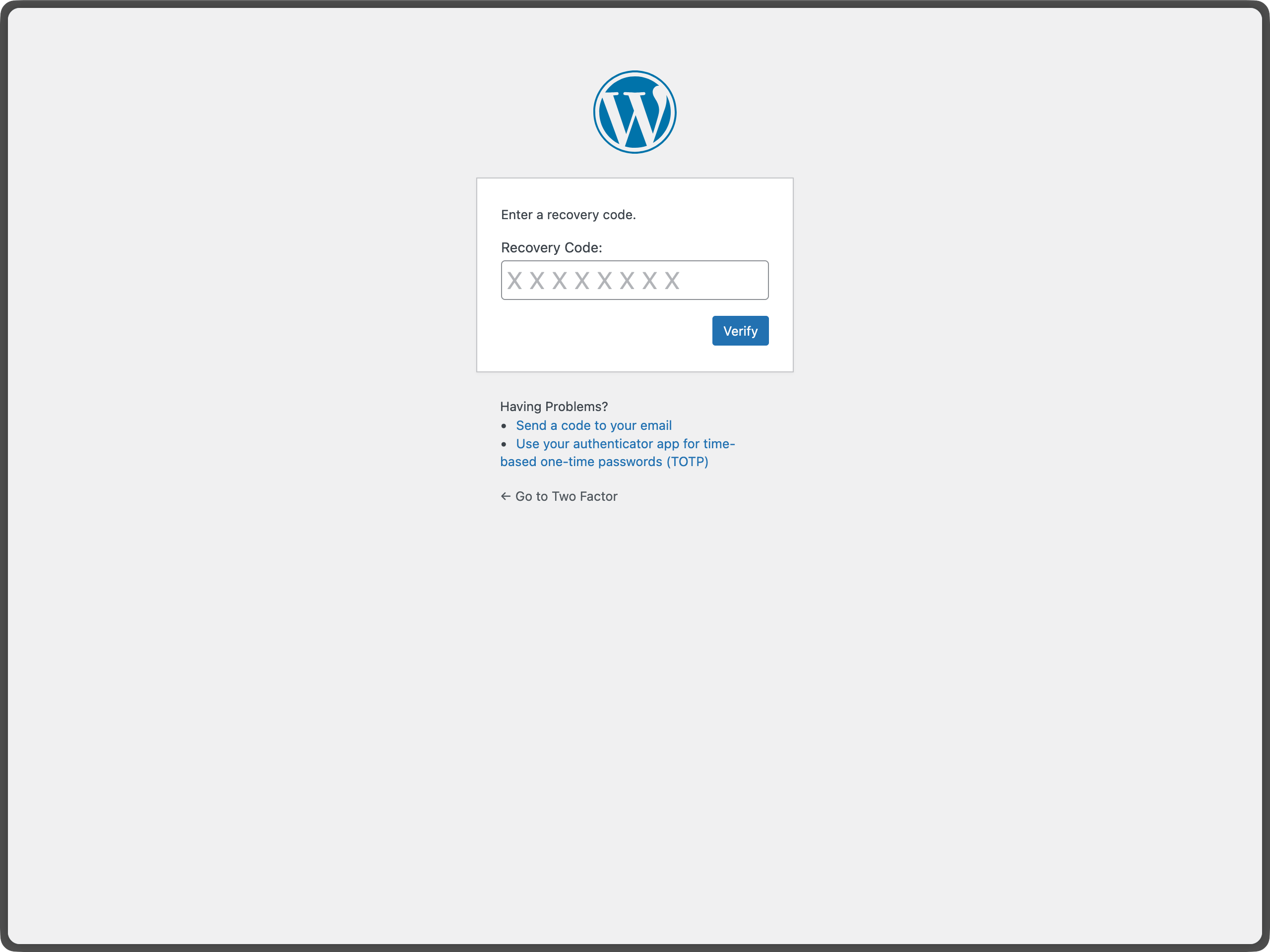
Authenticator App (TOTP) setup with QR code – Demonstrates the QR code generation and manual key entry for TOTP setup. 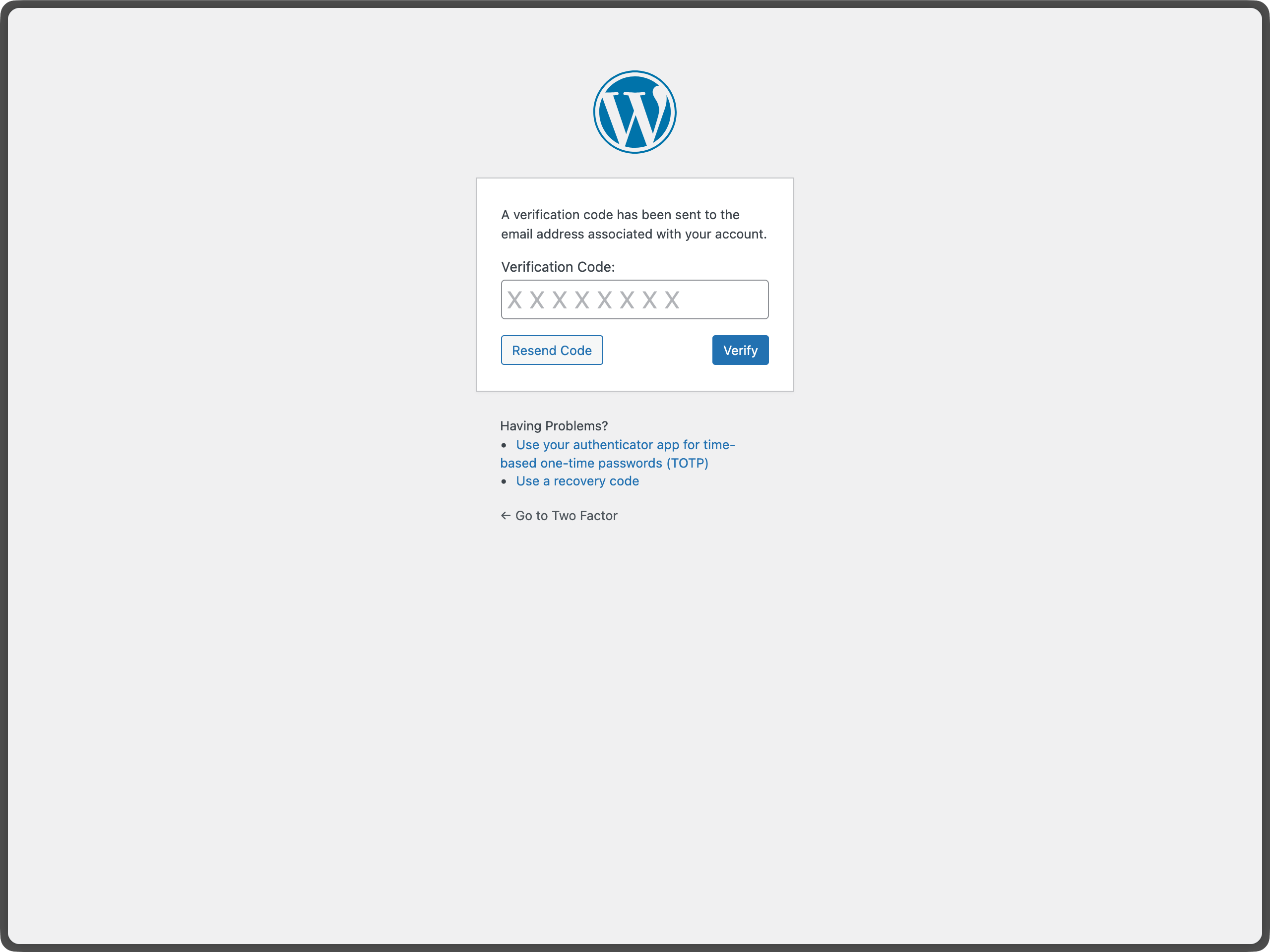
Backup codes generation and management – Shows the backup codes interface for generating and managing emergency access codes.
FAQ
-
Two-Factor プラグインはどのバージョンの PHP と WordPress をサポートしていますか ?
-
このプラグインは最新2つの WordPress メジャーバージョンとその WordPress がサポートする最小の PHP バージョン をサポートしています。
-
フィードバックを送信したり、バグに関するサポートを受けるには
-
バグ、機能の提案、その他セキュリティに関連しないフィードバックを報告するには、GitHub 上の Two Factor レポジトリのイシューを利用してください。新しいイシューを立てる際には、既存のイシューを検索し、他の誰かが同じフィードバックを報告していないかどうか確認してください。
-
セキュリティ関連のバグを報告するには
-
プラグイン開発チームおよび WordPress コミュニティは、セキュリティ関連のバグ対応を真摯に受け止めています。責任ある開示にご尽力いただいたことに感謝するとともに、そのご貢献を正式に認識できるよう最善を尽くします。
セキュリティの問題を報告するには、WordPress HackerOne プログラムにアクセスしてください。
-
What if I lose access to all my authentication methods?
-
If you have backup codes enabled, you can use one of those to regain access. If you don’t have backup codes or have used them all, you’ll need to contact your site administrator to reset your account. This is why it’s important to always enable backup codes and keep them in a secure location.
-
Can I use this plugin with WebAuthn?
-
The plugin previously supported FIDO U2F, which was a predecessor to WebAuthn. There is an open issue to add WebAuthn support here: https://github.com/WordPress/two-factor/pull/427
-
Is there a recommended way to use passkeys or hardware security keys with Two-Factor?
-
Yes. For passkeys and hardware security keys, you can install the Two-Factor Provider: WebAuthn plugin: https://wordpress.org/plugins/two-factor-provider-webauthn/
. It integrates directly with Two-Factor and adds WebAuthn-based authentication as an additional two-factor option for users.
評価
貢献者と開発者
Two-Factor はオープンソースソフトウェアです。以下の人々がこのプラグインに貢献しています。
貢献者変更履歴
0.16.0 – 2026-03-27
- Breaking Changes: Remove legacy FIDO U2F provider support by #439.
- New Features: Add a dedicated settings page for plugin configuration in wp-admin by #764.
- New Features: Add a support links filter so consumers can customize contextual recovery/help links by #615.
- New Features: Refresh backup codes UI styling and behavior by #804.
- Bug Fixes: Delete stored TOTP secrets when the TOTP provider is disabled by #802.
- Bug Fixes: Harden provider handling so login/settings checks do not fail open when expected providers disappear by #586.
- Bug Fixes: Ensure only configured providers are saved and enabled in user settings by #798.
- Bug Fixes: Improve settings-page accessibility and fix profile settings link behavior by #828 and #830.
- Bug Fixes: Resolve PHPCS violations in provider files by #851.
- Development Updates: Move login styles and provider scripts from inline output to enqueued/external assets by #807 and #814.
- Development Updates: Improve inline docs and static-analysis compatibility (WPCS/phpstan) by #810, #815, and #817.
- Development Updates: Improve unit test reliability and integrate CI code coverage reporting by #825, #841, and #842.
- Development Updates: Update readme docs and modernize CI workflow infrastructure by #835, #837, #843, and #849.
- Dependency Updates: Bump
qsfrom 6.14.1 to 6.14.2 by #794. - Dependency Updates: Bump
basic-ftpfrom 5.0.5 to 5.2.0 by #816. - Dependency Updates: Apply automatic lint/format updates and associated Composer package refreshes by #799.
0.15.0 – 2026-02-13
- Breaking Changes: Trigger two-factor flow only when expected by @kasparsd in #660 and #793.
- New Features: Include user IP address and contextual warning in two-factor code emails by @todeveni in #728
- New Features: Optimize email text for TOTP by @masteradhoc in #789
- New Features: Add “Settings” action link to plugin list for quick access to profile by @hardikRathi in #740
- New Features: Additional form hooks by @eric-michel in #742
- New Features: Full RFC6238 Compatibility by @ericmann in #656
- New Features: Consistent user experience for TOTP setup by @kasparsd in #792
- Documentation:
@sincedocs by @masteradhoc in #781 - Documentation: Update user and admin docs, prepare for more screenshots by @jeffpaul in #701
- Documentation: Add changelog & credits, update release notes by @jeffpaul in #696
- Documentation: Clear readme.txt by @masteradhoc in #785
- Documentation: Add date and time information above TOTP setup instructions by @masteradhoc in #772
- Documentation: Clarify TOTP setup instructions by @masteradhoc in #763
- Documentation: Update RELEASING.md by @jeffpaul in #787
- Development Updates: Pause deploys to SVN trunk for merges to
masterby @kasparsd in #738 - Development Updates: Fix CI checks for PHP compatability by @kasparsd in #739
- Development Updates: Fix Playground refs by @kasparsd in #744
- Development Updates: Persist existing translations when introducing new helper text in emails by @kasparsd in #745
- Development Updates: Fix
missing_direct_file_access_protectionby @masteradhoc in #760 - Development Updates: Fix
mismatched_plugin_nameby @masteradhoc in #754 - Development Updates: Introduce Props Bot workflow by @jeffpaul in #749
- Development Updates: Plugin Check: Fix Missing $domain parameter by @masteradhoc in #753
- Development Updates: Tests: Update to supported WP version 6.8 by @masteradhoc in #770
- Development Updates: Fix PHP 8.5 deprecated message by @masteradhoc in #762
- Development Updates: Exclude 7.2 and 7.3 checks against trunk by @masteradhoc in #769
- Development Updates: Fix Plugin Check errors:
MissingTranslatorsComment&MissingSingularPlaceholderby @masteradhoc in #758 - Development Updates: Add PHP 8.5 tests for latest and trunk version of WP by @masteradhoc in #771
- Development Updates: Add
phpcs:ignorefor falsepositives by @masteradhoc in #777 - Development Updates: Fix(totp):
otpauthlink in QR code URL by @sjinks in #784 - Development Updates: Update deploy.yml by @masteradhoc in #773
- Development Updates: Update required WordPress Version by @masteradhoc in #765
- Development Updates: Fix: ensure execution stops after redirects by @sjinks in #786
- Development Updates: Fix
WordPress.Security.EscapeOutput.OutputNotEscapederrors by @masteradhoc in #776 - Dependency Updates: Bump qs and express by @dependabot[bot] in #746
- Dependency Updates: Bump lodash from 4.17.21 to 4.17.23 by @dependabot[bot] in #750
- Dependency Updates: Bump lodash-es from 4.17.21 to 4.17.23 by @dependabot[bot] in #748
- Dependency Updates: Bump phpunit/phpunit from 8.5.44 to 8.5.52 by @dependabot[bot] in #755
- Dependency Updates: Bump symfony/process from 5.4.47 to 5.4.51 by @dependabot[bot] in #756
- Dependency Updates: Bump qs and body-parser by @dependabot[bot] in #782
- Dependency Updates: Bump webpack from 5.101.3 to 5.105.0 by @dependabot[bot] in #780
0.14.2 – 2025-12-11
- New Features: Add filter for rest_api_can_edit_user_and_update_two_factor_options by @gutobenn in #689
- Development Updates: Remove Coveralls tooling and add inline coverage report by @kasparsd in #717
- Development Updates: Update blueprint path to pull from main branch instead of a deleted f… by @georgestephanis in #719
- Development Updates: Fix blueprint and wporg asset deploys by @kasparsd in #734
- Development Updates: Upload release only on tag releases by @kasparsd in #735
- Development Updates: Bump playwright and @playwright/test by @dependabot[bot] in #721
- Development Updates: Bump tar-fs from 3.1.0 to 3.1.1 by @dependabot[bot] in #720
- Development Updates: Bump node-forge from 1.3.1 to 1.3.2 by @dependabot[bot] in #724
- Development Updates: Bump js-yaml by @dependabot[bot] in #725
- Development Updates: Mark as tested with the latest WP core version by @kasparsd in #730
0.14.1 – 2025-09-05
- Don’t URI encode the TOTP url for display. by @dd32 in #711
- Removed the duplicate Security.md by @slvignesh05 in #712
- Fixed linting issues by @sudar in #707
- Update development dependencies and fix failing QR unit test by @kasparsd in #714
- Trigger checkbox js change event by @gedeminas in #688
0.14.0 – 2025-07-03
- Features: Enable Application Passwords for REST API and XML-RPC authentication (by default) by @joostdekeijzer in #697 and #698. Previously this required two_factor_user_api_login_enable filter to be set to true which is now the default during application password auth. XML-RPC login is still disabled for regular user passwords.
- Features: Label recommended methods to simplify the configuration by @kasparsd in #676 and #675
- Documentation: Add WP.org plugin demo by @kasparsd in #667
- Documentation: Document supported versions of WP core and PHP by @jeffpaul in #695
- Documentation: Document the release process by @jeffpaul in #684
- Tooling: Remove duplicate WP.org screenshots and graphics from SVN trunk by @jeffpaul in #683
