ROX-10304: Remove NoValidRole error sentinel#1409
Conversation
…ntViolation, ErrNoCredentials, ErrNoValidRole, ErrNotAuthorized, ErrNoAuthzConfigured
|
Tag for build #486192 is 💻 For deploying this image using the dev scripts, run the following first: export MAIN_IMAGE_TAG='3.69.x-556-g91bf9b4558'🕹️ A |
pkg/grpc/authn/interceptor.go
Outdated
| // Only service identities can have no roles assigned. | ||
| if len(id.Roles()) == 0 && id.Service() == nil { | ||
| return context.WithValue(ctx, identityErrorContextKey{}, errox.GenericNoValidRole()), nil | ||
| return context.WithValue(ctx, identityErrorContextKey{}, errox.NotAuthorized.CausedBy("no valid role")), nil |
There was a problem hiding this comment.
| return context.WithValue(ctx, identityErrorContextKey{}, errox.NotAuthorized.CausedBy("no valid role")), nil | |
| return context.WithValue(ctx, identityErrorContextKey{}, errox.NotAuthorized.CausedBy("only service identities can have no roles assigned")), nil |
pkg/grpc/authz/user/role.go
Outdated
| func (p *roleChecker) checkRole(roleNames []string) error { | ||
| if len(roleNames) == 0 { | ||
| return errox.NoValidRole | ||
| return errox.NotAuthorized |
There was a problem hiding this comment.
how about adding more context here e.g.
| return errox.NotAuthorized | |
| return errox.NotAuthorized.CausedBy("no roles assigned to the user")) |
| userRoles := userInfo.GetRoles() | ||
| if len(userRoles) == 0 { | ||
| err := errox.GenericNoValidRole() | ||
| err := errox.NotAuthorized.CausedBy("no valid role for the user") |
There was a problem hiding this comment.
How about adding explicit information about missing roles. no valid role sounds like there are some roles but not valid for this situation
| err := errox.NotAuthorized.CausedBy("no valid role for the user") | |
| err := errox.NotAuthorized.CausedBy(fmt.Sprintf("%s has no roles", userInfo.GetFriendlyName())) |
There was a problem hiding this comment.
I believe 401 is the right choice of error here, see https://issues.redhat.com/browse/ROX-8092 including comments. cc @rhybrillou
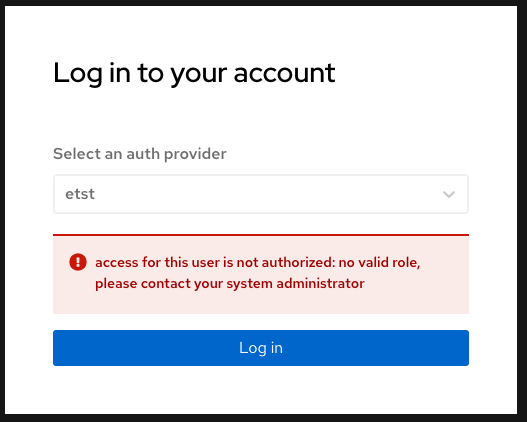
I'd suggest to introduce a new sentinel error in pkg/grpc/auth, maybe in none.go or in a new file, that will replace both NoValidRole and GenericNoValidRole(), e.g.
ErrNoValidRole := errox.NoCredentials.New("access for this user is not authorized: no valid role," +
" please contact your system administrator")
…ROX-10304-remove-generic-no-valid-role-error
pkg/auth/role/error.go
Outdated
| @@ -0,0 +1,11 @@ | |||
| package role | |||
There was a problem hiding this comment.
Maybe put this file directly into pkg/auth/? This way we avoid having a auth/role package with just an error definition and the call sites look sleeker: auth.ErrNoValidRole.
 md2119
left a comment
md2119
left a comment
There was a problem hiding this comment.
The changes are fine, but is there an easy way for developers to look for sentinal values, especially if they are scattered in different pkgs?
…ROX-10304-remove-generic-no-valid-role-error
|
| GitGuardian id | Secret | Commit | Filename | |
|---|---|---|---|---|
| 3038029 | Generic High Entropy Secret | 138264d | qa-tests-backend/src/main/groovy/services/NotifierService.groovy | View secret |
| 3038029 | Generic High Entropy Secret | c751bce | qa-tests-backend/src/main/groovy/services/NotifierService.groovy | View secret |
🛠 Guidelines to remediate hardcoded secrets
- Understand the implications of revoking this secret by investigating where it is used in your code.
- Replace and store your secrets safely. Learn here the best practices.
- Revoke and rotate these secrets.
- If possible, rewrite git history. Rewriting git history is not a trivial act. You might completely break other contributing developers' workflow and you risk accidentally deleting legitimate data.
To avoid such incidents in the future consider
- following these best practices for managing and storing secrets including API keys and other credentials
- install secret detection on pre-commit to catch secret before it leaves your machine and ease remediation.
🦉 GitGuardian detects secrets in your source code to help developers and security teams secure the modern development process. You are seeing this because you or someone else with access to this repository has authorized GitGuardian to scan your pull request.
Our GitHub checks need improvements? Share your feedbacks!
For global sentinels — for sure, but you already know that : ). For package-level sentinels, we can say that those changing or using a package shall be able to discover errors defined in that package but I think your comment is valid. Maybe we can have a gentlemen's agreement (and a linter) that all package sentinels must be defined in |
Description
Removed
GenericNoValidRoleerror. We have added new Error sentinel inpkg/auth/role.Note: This PR is based on
mtodor/ROX-10303-replace-new-error-wrappersbranch. After PR #1389 is merged, we will change the base branch.Checklist
[ ] Unit test and regression tests added- nothing is added[ ] Evaluated and added CHANGELOG entry if required- not relevant[ ] Determined and documented upgrade steps- nothing relevant for upgrade steps[ ] Documented user facing changes (create PR based on stackrox/openshift-docs and merge into rhacs-docs)- no user-facing changesTesting Performed
1. Compare in UI - No change - no change
2. REST request with token without Role - no change
3. Request with not Admin role: - no change
Additionally, default checks are also done:
make imageworksmake styleworks so that the linting of all go files is correct