May
2
2010
From time to time I just blast tweets about software development, project planning, team dynamics, or whatever else comes to mind. Here is a synopsis of recent tweets and rants. If you want to follow the conversation follow me at techknow and/or juixe and I’ll be sure to follow back.
Software Development
- Any software feature request should be broken down to 90% thinking and 10% coding.
- Multiple-touch is the greatest things since buttons.
- If a developer fools you once, shame on you, because they are usually fooling themselves when it comes to giving accurate estimates.
- Don’t take developers estimate at face value.
- Recommend The Rubyist for the Developers Directory on Tumblr: http://www.tumblr.com/directory/recommend/developers/rubyist
- Many non-programming software users don’t understand the meaning of concatenated or null so don’t use these in labels in your UI.
- I like to provide solutions that don’t involve complaining.
- If Heraclitus is right and you never step in the same river twice, then you never write the same program twice.
- Bugs keep my code humble.
- A bug’s ingenuity is proportional to a developer’s ego and self importance.
- Bugs like to in build nests out of spaghetti code in untested corner cases.
- Working running code is just one corner case.
- I use dead laptop drives as coasters.
- My emotions are user generated.
- I om nom nom nom on memes.
- The interweb is my inspiration.
- I CAN HAZ DREAMS OF INTERWEB MEMES
Team Leadership
- When life gives you lemons, you may make lemonade. When life gives me lemons, I make myself some limoncello.
- New motto/slogan: Don’t be a robot, unless you are 20 feet tall and can transform into a fighter jet.
- Dream big or wake up.
- The Law of Big Consequences: Large consequences are often the effect of making considerable decisions in a big rush.
- Laughter is the duct tape equivalent of emotions, it can be used to patch up bad feelings or misunderstandings.
- Manual, Error Prone, Time Consuming. Pick none!
- When people dig their own hole they can’t get out of it by digging deeper.
- Fight the power, and fight the hype.
- A key skill in life is to know when to end a conversation.
- Nothing is how you thought of it originally, it is up to you to make it better.
- If you have time to lean, you have time to clean.
Product Placement
- Amazon knows what books you bought for the Kindle, how often and for how long you read, can add and remove books, and read your bookmarks, notes, and highlights…
- FaceBook, Inc = F.B.I.
- Apple wants to design multiple-touch devices, Google wants to crawl content, Facebook wants to own your social graph and associated data.
- Facebook is really dumbing down the web with the like button.
- Facebook’s Open Graph is not really open. If you don’t own the platform, can look through the source, can own the data it is not open!
- Did someone just unlocked the Foursquare Sellout Badge at Yahoo HQ!
- I’ve had enough Lifetime movies for one lifetime.
- The world according Ronald McDonald is made out of corn meal.
- The McChicken nugget is the worst thing since sliced bread.
- Peeps are the most disgusting artificial food product.
Qoute
- One good thing about music, when it hits you, you feel no pain. – Bob Marley
- I don’t like negotiating with people I can’t beat up. – Goldberg
- We live in an amazing world and it’s wasted on the crappiest generation. – Louis C.K.
- Beware of artists they mix with all classes of society and are therefore most dangerous. – Queen Victoria
- He eyes are the nipples of the face. -The House Bunny
no comments | tags: apple, bugs, coding, computer, development, error, facebook, interweb, kindle, meme, Programming, rubyist, software | posted in Programming, Rant, TechKnow
May
1
2010
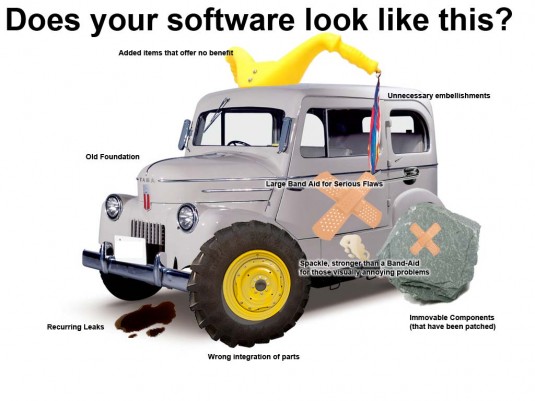
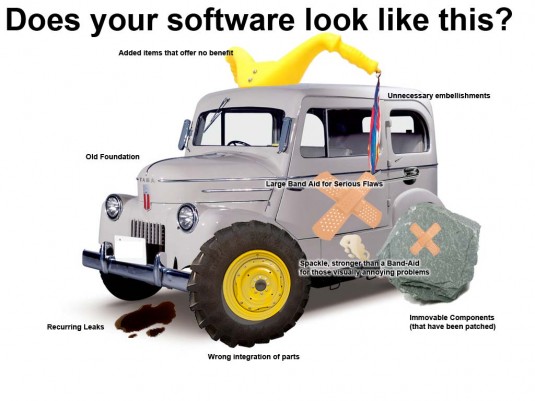
In a typical day, software engineers, use diagrams, charts, and a ideograms to represent the software systems we work on. The biggest problems with software can also be described visually, such as the following image which tries to explain problems of software engineering.
Software Engineering Explained
When software engineering is that complicated, just imagine how the software application produced in such an environment looks like.
How Software Looks Like
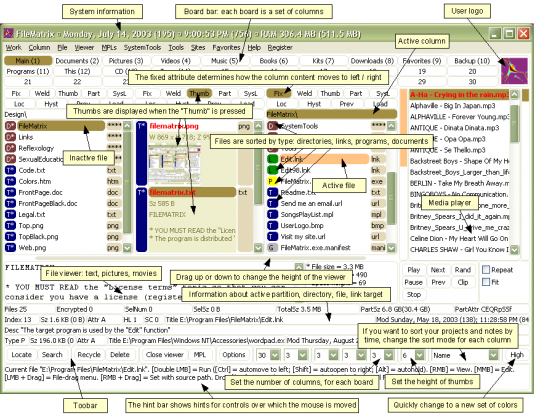
Creating a clean, simply to use, functional application is harder than you think. Only a few companies have been successful with simplicity. Most enterprise applications look like a mosaic of buttons and text fields.

Stuff That Happens UI
Here is a screen shot showing the complexity of a software application.
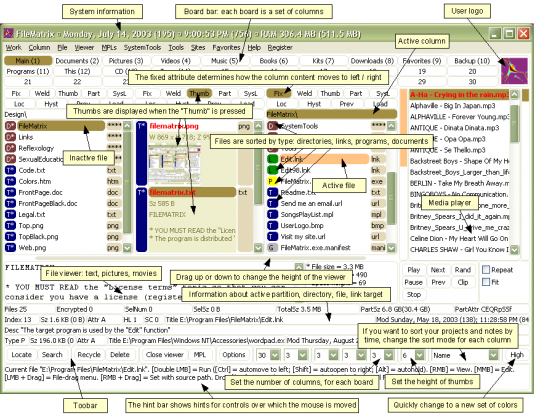
FileMatrix UI Complexity
If you have any images, graphics, diagrams, or charts that illustrate the complexity of software engineering feel free to share in the comments.
1 comment | tags: application, development, diagram, engineering, Programming, software, ui, ux | posted in Programming, Rant, TechKnow
Apr
23
2010
Rasmus Lerdorf, the Danish creator of the PHP programming language, recently tweeted the following bit of hubris.
For all the folks getting excited about my quotes. Here is another – Yes, I am a terrible coder, but I am probably still better than you :)
That sounds like something that DHH would say, who also happens to be a Danish programmer. In one hand he did invent a new programming language, in the other it was PHP. In one hand he made web programming accessible to thousands of developer, in the other hand the code produced by most of these developers is unreadable and unmanageable.
Of course, a great many folks took the troll bait and commented on the validity of the tweet. My favorite comment was from
Entropy on Reddit.
Kenny G plays the saxophone better than I do, but that provides little solace for his countless victims.
I was not able to find additional background to this tweet, but I can only imagine he tweeted it in good fun, and not in my milkshake brings all the developers to the yard, and their like, it’s better than yours.
no comments | tags: coder, dhh, hubris, lol, PHP, Programming, Rasmus, twitter | posted in Programming, Rant, TechKnow
Apr
12
2010
A use case is just one corner case, and developers working with code very often test just for that one corner case. A corner case can be described as a program error or software bug that occurs outside of normal use, or caused by parameter values and environments outside the intended acceptable range. I’ve learned that corner cases are more common than what developers like to admit, so much so that working code is just another corner case.
In my experience, the number one source of corner cases are assumptions hard code and baked into the source code, like assuming that your users have five digit zip codes, or use an English alphabet, or are based in a specific timezone, etc. Sometimes corner cases arise because someone cut a corner, didn’t check if an input parameter fit a certain criteria, was of a specific format, length, or within an acceptable range. Yet with all the assumptions we inadvertently leave behind in our code, I’ve seen developers take great offense and defend their code with the fervor of a religious zealot by saying, “you are not supposed to enter non-numeric values.” Even with the most stringent process and under tight deadlines, developers have been known to regress to the “if it compiles, ship it” mentality. You can cut corners in the design and implementation of a software program, but you most often will not cut the corner cases where bugs like to linger, hide, and build nests out of code. The number of corner cases is proportional to the complexity of an application.
2 comments | posted in Programming, Rant, TechKnow
Apr
6
2010
From time to time I just blast tweets about software development, project planning, team dynamics, or whatever else comes to mind. Here is a synopsis of recent tweets and rants. If you want to follow the conversation follow me at techknow and/or juixe and I’ll be sure to follow back.
Software Development
- Security pet peeves: captchas, security questions, having to login after changing my password.
- A supercomputer won’t solve the incompetence of bad programmers on a deadline.
- All software is in beta.
- The Like button needs to be killed.
- \-: “premature optimization is root all of evil.” (-: “That’s what she said.”
- This must be a record. I just improved our app’s memory consumption by 80%, some 400MB, by changing one line of code.
- I love technology because I can now blame my misspelling on my iPhone.
- Where 2.0 is the new meme. Is your website Where 2.0 aware?
- Building a community and building a business around a community are not the same thing.
- The linked list was recently patented, I’m going to patent something critical to civilization, like calculus or pottery.
- Dear debugger, I wish you could introspect my feelings and put a breakpoint on my heart break.
- A slew of computer bugs are caused by assumptions made by the programmer.
- You know things are bad when you get error code 0000.
- Bugs grow organically.
- It is possible to make spaghetti code out of Obeject Oriented Programmmmmming?
- Rule of thumb: use immutable objects as keys to hash maps otherwise get to you your debugger.
Team Leadership
- The best ideas are free.
- No matter what, you will never be less busy.
- Let’s be honest, anywhere from 10-30% of a resume is a stretch.
- So as not to forget anything, remember nothing.
- When you give someone else time, you waste you own.
- Don’t give any answer, give the right question.
- If you have a one trick pony, ride it until it is ready to be put to pasture.
- Problems are meant to be solved only if they can’t be ignored.
- The one best possible thing you can do to make any situation better is to not make it worse.
- One can lead by asking questions, just as well as giving orders.
- If you build it, they will come. But if you make it to complex or change it to often, then they will leave.
- The secret ingredient is to believe there is a secret ingredient.
- I don’t express myself best when speaking, but when reflecting.
- Praying may not change the world, but it can change your perspective which is helpful to change your world.
- Folks usually want the what first but I think that the why and the how is more important than the what.
Product Placement
- Facebook announced a major investment by the CIA. It was reported that the US Gov will push for Facebook Connect as a National ID program.
- PayPal just sucks. I can transfer money to former Soviet Bloc countries faster than I can between PayPal and my bank.
- Spam is like a staple in Hawaii. So it comes as no surprise that Mahalo is one of the most spam ridden sites online.
- My suggestion to cable companies: give away basic cable to every American with on demand features. Add value outside the cable box.
- Which will provide better value/info for businesses, yelp or foursquare?
- The current Apple Appstore approval time is rand() * Months.
- McDs should make a tofu McMuffin.
- A sign at a Palo Alto church: redeem your soul, there is an app for that.
- Purple Cow Thinking: don’t be boring, safe is risky, design rules now, very good is bad.
Quote
- If there is a limit, you should, you must test it. – Seth Godin/Purple Cow
- Vision without execution is hallucination – Thomas Edison
- Success is not the key to happiness. Happiness is the key to success. If you love what you are doing, you will be successful. – Herman Cain
1 comment | tags: apple, bugs, development, error, facebook, paypal, Programming, security, software, tofu | posted in Programming, Rant, TechKnow
Mar
30
2010
I’ve always been interested in understanding common programming errors so that I can easily recognize and diagnose problems, hopefully without spending hours staring at my breakpoints in my debugger. Previously, I’ve written on Common Groovy Errors and Top Worse Java Errors.
The US Department of Homeland Security, under the Common Weakness Enumeration initiative put out the 2010 CWE/SANS Top 25 Most Dangerous Programming Errors. Most of the errors noted related to web application security programming errors.
- Failure to Preserve Web Page Structure (‘Cross-site Scripting’)
- Improper Sanitization of Special Elements used in an SQL Command (‘SQL Injection’)
- Buffer Copy without Checking Size of Input (‘Classic Buffer Overflow’)
- Cross-Site Request Forgery (CSRF)
- Improper Access Control (Authorization)
- Reliance on Untrusted Inputs in a Security Decision
- Improper Limitation of a Pathname to a Restricted Directory (‘Path Traversal’)
- Unrestricted Upload of File with Dangerous Type
- Improper Sanitization of Special Elements used in an OS Command (‘OS Command Injection’)
- Missing Encryption of Sensitive Data
- Use of Hard-coded Credentials
- Buffer Access with Incorrect Length Value
- Improper Control of Filename for Include/Require Statement in PHP Program (‘PHP File Inclusion’)
- Improper Validation of Array Index
- Improper Check for Unusual or Exceptional Conditions
- Information Exposure Through an Error Message
- Integer Overflow or Wraparound
- Incorrect Calculation of Buffer Size
- Missing Authentication for Critical Function
- Download of Code Without Integrity Check
- Incorrect Permission Assignment for Critical Resource
- Allocation of Resources Without Limits or Throttling
- URL Redirection to Untrusted Site (‘Open Redirect’)
- Use of a Broken or Risky Cryptographic Algorithm
- Race Condition
no comments | tags: code, debugging, error, homeland, Programming, security, SQL, webapp, xss | posted in PHP, Programming, TechKnow